CILLA ransomware is a file locking threat that tries to imitate Maoloa virus
CILLA ransomware is a file locking virus that stems from GlobeImposter 2.0 malware family
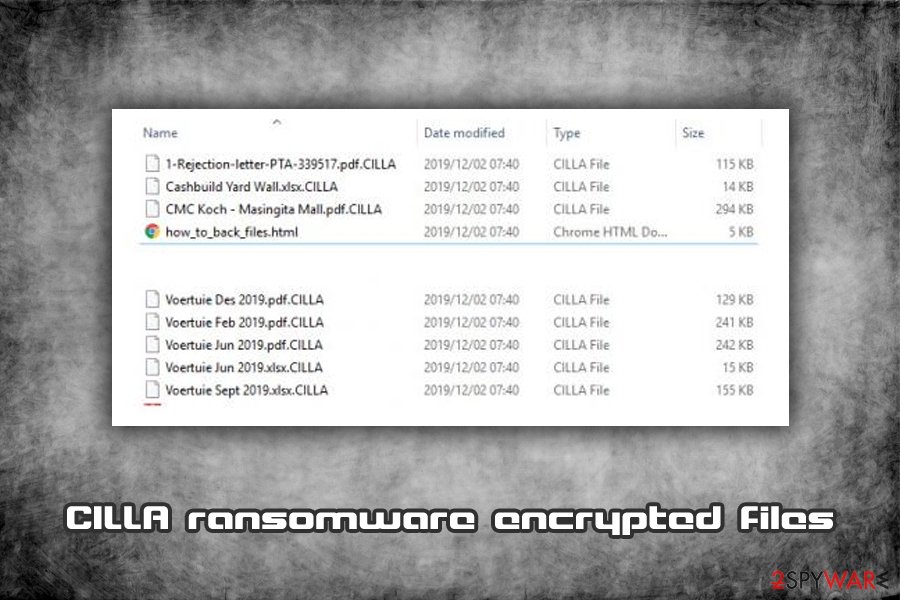
CILLA ransomware is a type of malware that focuses on money extortion and comes from a well-known malware family – GlobeImposter 2.0. Soon after infiltration, the virus encrypts all pictures, videos, documents, and other data by using a strong encryption algorithm AES-256[1] and appends .CILLA extension to each of the files. To retrieve the access to data, users are asked to email hackers via [email protected] or [email protected] and pay a ransom in Bitcoin, the amount of which is not stated in the ransom note how_to_back_files.html.
Unlike most file locking viruses, CILLA ransomware tries to imitate another crypto-locking malware Maola – it is done deliberately to prevent security experts from identifying the infection correctly. Nevertheless, this does not make any difference to the affected users, as a result in both cases is the same – locked data. Unfortunately, there is no CILLA ransomware decryptor currently available, although there are other methods that might be able to help you recover your files.
| Name | CILLA ransomware |
| Type | File locking virus, crypto-malware |
| Family | CILLA is a variant of GlobeImposter 2.0 ransomware |
| Encryption algorithm | AES-256 is used to encode pictures, music, videos, documents, databases and other files located on local and networked drives |
| File extension | Each of the locked files is marked with .CILLA extension, for example, schedule.xlsx is turned into schedule.xlsx.CILLA |
| Ransom note | The malware drops a how_to_back_files.html ransom note into most of the folders on the affected machine (where the encrypted files are located) |
| Contact | Crooks ask to contact them via [email protected] or [email protected] to negotiate the payment process |
| Ransom size | The ransom amount is not provided in the ransom note, although previous variants of malware are known to ask for as much as 10 Bitcoin for the decryption tool |
| Known incidents | The malware locked all files on Food Bank’s computers in June 2019 |
| Removal | Employ reputable anti-malware software and perform a full system scan (entering Safe Mode might be necessary sometimes) |
| Recovery | After the malware is eliminated, users might experience system crashes and errors due to virus damage. To fix these issues, we recommend using repair software Reimage Reimage Cleaner |
| File decryption |
Unfortunately, there is no CILLA ransomware decryption tool available. There are only three other ways to recover data:
|
Just as any other large ransomware family member, CILLA ransomware is spread with the help of various methods, including:
- Spam emails
- Exploit kits[2]
- Software cracks
- Pirated software installers
- Unprotected RDP connections
- Fake updates, etc.
In some cases, malicious actors are also known to insert a legitimate program Process hacker or Process Hacker 2 into the infected system in order to monitor it and perform other malicious activities. Nevertheless, this unwanted activity can be detected and stopped by most of the up-to-date security tools, which can also help with CILLA removal.
Once CILLA ransomware gets into the machine, it starts the preparation for the file encryption process. For example, it deletes several files (such as Windows’ automatic file backups) and modifies the Windows registry to run without interruptions. After that, the virus targets the most common file types like .doc, .html, .jpg, .mp4, .ppt, and others, all while skipping executables, as well as system files.
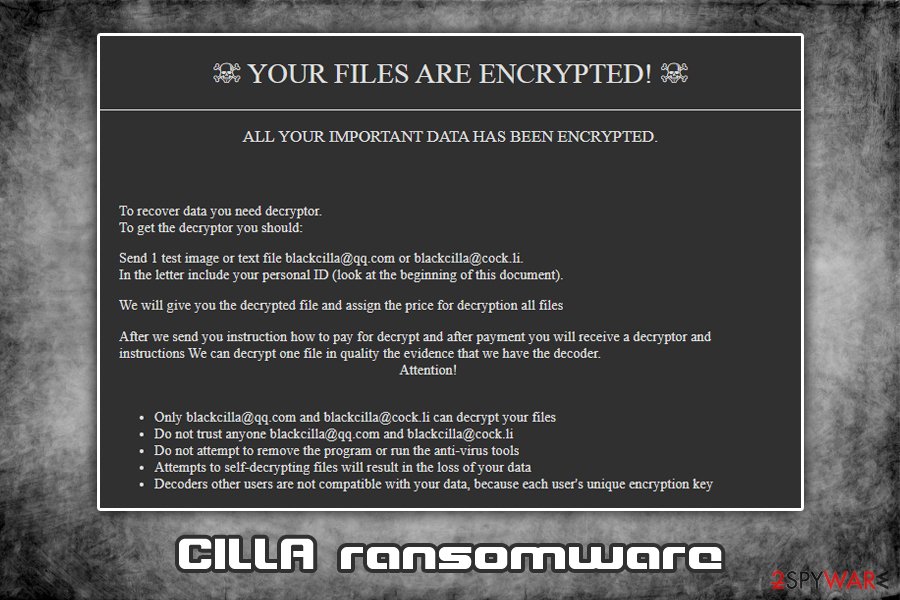
The dropped ransom note how_to_back_files.html states the following:
☠ YOUR FILES ARE ENCRYPTED! ☠
ALL YOUR IMPORTANT DATA HAS BEEN ENCRYPTED.To recover data you need decryptor.
To get the decryptor you should:
Send 1 test image or text file [email protected] or [email protected].
In the letter include your personal ID (look at the beginning of this document).We will give you the decrypted file and assign the price for decryption all files
After we send you instruction how to pay for decrypt and after payment you will receive a decryptor and instructions We can decrypt one file in quality the evidence that we have the decoder.
Attention!Only [email protected] and [email protected] can decrypt your files
Do not trust anyone [email protected] and [email protected]
Do not attempt to remove the program or run the anti-virus tools
Attempts to self-decrypting files will result in the loss of your data
Decoders other users are not compatible with your data, because each user’s unique encryption key
As evident, the crooks are trying to intimidate victims and make them pay the ransom. However, security experts[3] do not recommend contacting cybercriminals, as there is no guarantee that they will send required decryption software after the payment in Bitcoin. Additionally, paying crooks behind the CILLA virus will only fuel their will to produce more advanced viruses and infect more users.

CILLA ransomware is a type of virus that focuses on money extortion after locking all personal files on the infected device
While it is true that, in some cases, the files might get damaged after you remove CILLA ransomware, there is a solution for that. Before you do anything, you should backup all the encrypted data and then access Safe Mode to get rid of the virus with the help of reputable security software that can recognize the threat. According to Virus Total,[4] most security tools should be able to detect and eliminate the infection. CILLA ransomware is identified as follows:
- HEUR/AGEN.1011584
- Win32:Trojan-gen
- Ransom:Win32/Filecoder.RB!MSR
- Ransom_FAKEGLOBE.SMB
- Generic.Ransom.GlobeImposter.4361C1A9
- Heuristic.HEUR/AGEN.1011584, etc.
After that, you can try using third-party recovery tools to retrieve .CILLA encrypted files. If you are having Windows system issues after the infection, instead of reinstalling the OS, you could also run a scan with Reimage Reimage Cleaner .
There are several ways to protect yourself from ransomware intrusion
Some cybercriminals are implementing various methods when it comes to the illegal ransomware business. One thing is clear: ransomware is on the rise, and there are multiple hacking groups with highly established networks – these gangs infect thousands of users worldwide, as well as various businesses and organizations, resulting in millions of dollars in repair costs. While it is impossible to avoid ransomware completely, however, there are several ways to diminish that chance to a minimum.
The first step for a more secure computer is automated protection – anti-malware software. There are plenty of security tools available, and most of them even employ a separate feature that enables ransomware protection (so make sure it is always on). However, defenses provided by anti-malware software are never enough, and you should also be very careful when spending time online, opening emails, and downloading files. Here’s what to do to increase your PC security level:
- Do not open spam email attachments (files that ask you enable macros are most likely viruses) or click on hyperlinks inside;
- Patch your Windows OS along with all the installed software immediately when the updates are available;
- Avoid visiting high-risk websites like torrents, porn, gambling, etc. (if you do, enable ad-block for extra protection);
- Do not download and use software cracks or pirated program installers;
- Use strong passwords for all your accounts and never reuse them. Also, enable two-factor authentication where possible;
- Backup all your files as required;
To conclude, a combination of careful web browsing habits and comprehensive security solutions should be enough to keep even the most dangerous malware away.
Once CILLA ransomware locks the data, retrieving it is almost impossible unless ransom is paid and crooks provide a working decryption tool
Do not listen to cybercriminals and remove CILLA ransomware immediately
As already mentioned, it is true that CILLA ransomware removal might compromise the encrypted data permanently. To prevent that, you should immediately copy all the files to an external drive (flash USB or external HDD) or virtual drive (Google Drive, OneDrive, Dropbox, etc.). Once that is done, you need to ensure that you remove CILLA ransomware correctly.
It is not uncommon for crypto-malware to disable anti-virus software like Microsoft Defender. In such a way, hackers might prevent users from getting rid of the malicious payload and attempting alternative data recovery methods. In such a case, you should access Safe Mode with Networking and scan the machine with anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes and get rid of CILLA virus infection.
For .CILLA file recovery, you can either refer to the section below for various methods (keep in mind that chances of retrieving locked files with recovery software are relatively low) and risk your money and pay criminals for a decryption key, which is not recommended.
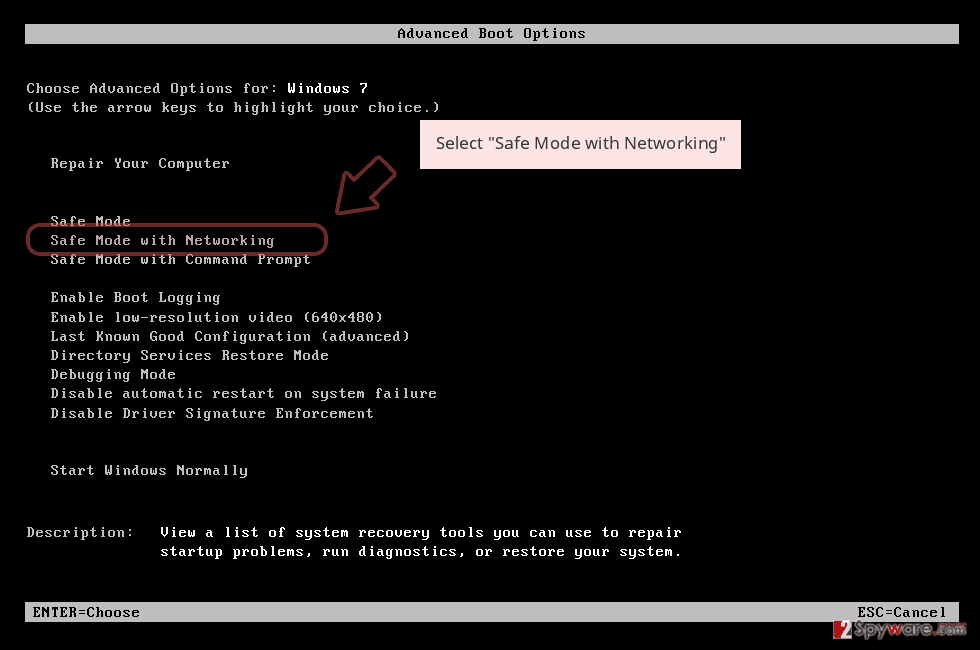
Remove CILLA using Safe Mode with Networking
If the virus prevents your security software from working correctly, enter Safe Mode with Networking:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
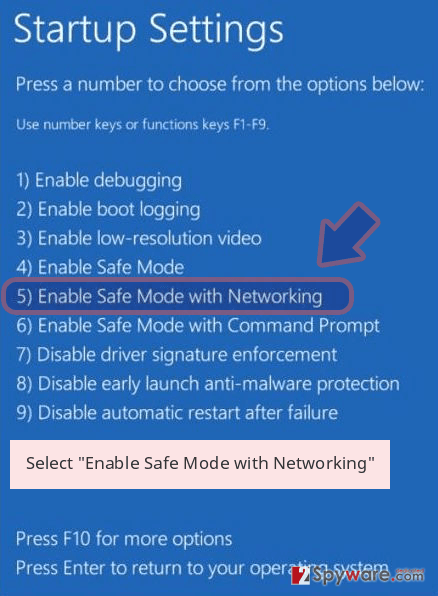
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete CILLA removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove CILLA using System Restore
You can also apply the Safe Mode for CILLA ransomware removal:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove CILLA from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by CILLA, you can use several methods to restore them:
Data Recovery Pro solution might be useful to some
While it is highly unlikely you can recover all the locked data with Data Recovery Pro, there is a chance you might get at least some of your files back.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by CILLA ransomware;
- Restore them.
Make use of Windows Previous Versions feature
This method can only function if you had System Restore enabled before.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer method might save your files
CILLA virus is programmed to delete Shadow Volume Copies. If this process fails, you have a high chance of recovering all your files with ShadowExplorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from CILLA and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2019-12-04 at 06:10 and is filed under Ransomware, Viruses.

