CovidWorldCry ransomware is coronavirus-themed malware that encrypts personal and some system files on the host machine
CovidWorldCry ransomware is a file locking virus that is spread via Rig Exploit kit
CovidWorldCry ransomware is a file locking virus that is spread via Rig Exploit kit
CovidWorldCry ransomware, otherwise known as BigLock or CoronaLock, is a data locking virus that was first spotted by security researcher GrujaRS[1] in late May 2020 and has not been attributed to any previously-known malware family. It uses ChaCha + AES encryption algorithms to lock all pictures, music, videos, documents, databases, and other personal files on the infected machine and its networks. It then demands a ransom in Bitcoin for the data release, which is only possible with a ransomware decryption tool in hackers’ possession.
CovidWorldCry ransomware has been released in two different versions:
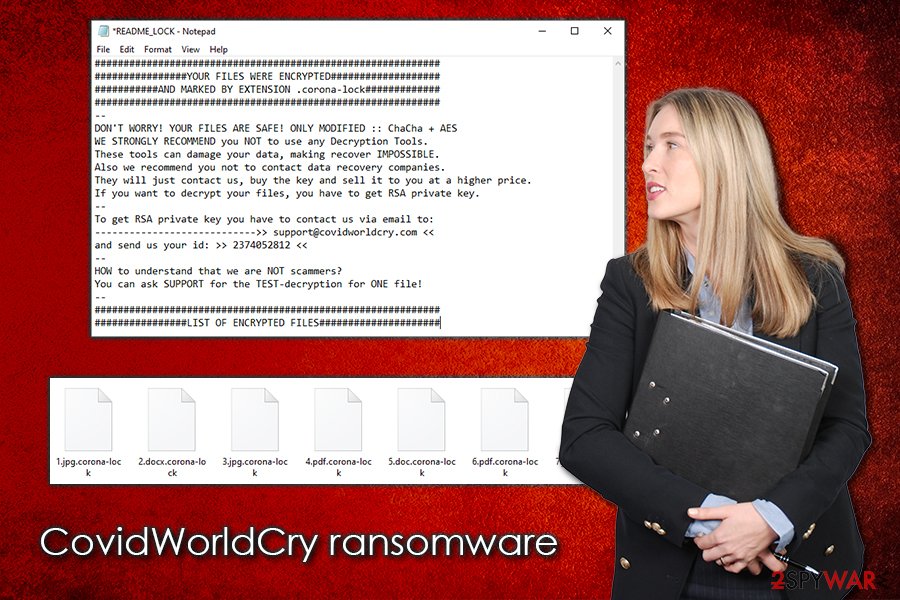
- Initial version appended .biglock extension to all files and dropped !!!READ_ME!!!.TXT ransom note (no contact email was provided);
- The second version, which showed up a few days later, delivered README_LOCK.TXT ransom note and used a .corona-lock marker (provided contact email [email protected]).
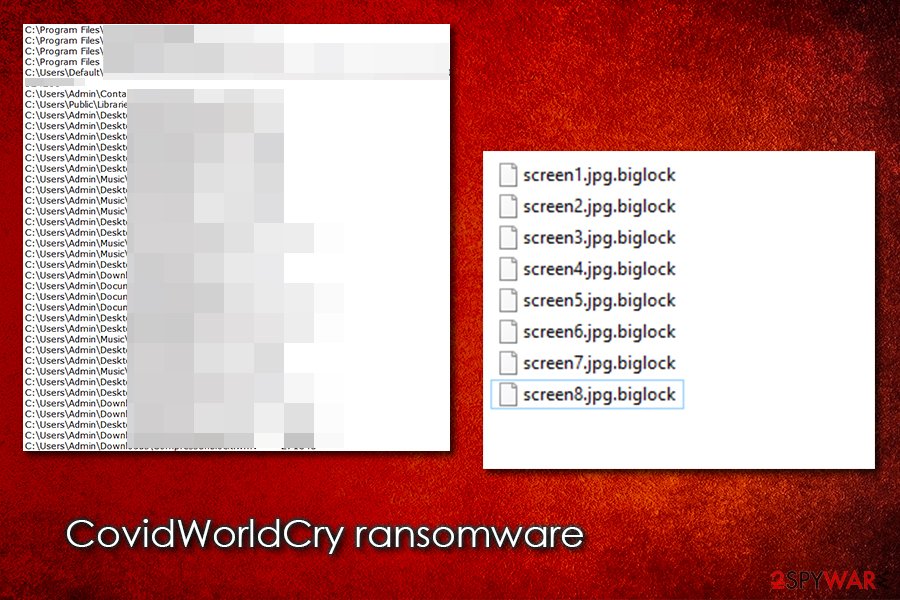
While most other malware of such type encrypts only user-related files, the CovidWorldCry virus encrypts some boot and system files, which is very unusual for ransomware. While it is extremely difficult to retrieve encrypted data without backups, paying the attackers is not recommended due to the possibility of being scammed.
| Name | CovidWorldCry ransomware |
| Type | Cryptomalware, file locking virus |
| Also known as | CoronaLock ransomware, Corona-Lock ransomware, BigLock ransomware |
| Distribution | Has been seen delivered via Rig exploit kit, although other methods, such as email spam, fake updates, etc., can be used as well |
| Related files | 2020-05-22_17-36-19.exe |
| File extension | Malware appends most of files on the system with .biglock or .corona-lock marker. Examples of encrypted files: “picture.jpg.biglock,” “document.doc.corona-lock |
| Ransom note | !!!READ_ME!!!.TXT or README_LOCK.TXT |
| Contact | Threat actors ask users to contact them via [email protected] email |
| Detection | Ransom:Win32/Coronalock.DEA!MTB, Win32:Malware-gen, PWS:Win32/Stealer.KM!MTB, A Variant Of Win32/Kryptik.HDOJ, Trojan Horse, TR/AD.RansomHeur.eku, Trojan.Win32.DelShad.dfc (Virus Total results) |
| Attributes | Encrypts personal files and demands ransom; deletes shadow volume copies and disables Windows recovery functions; copies sensitive data to a remote server for later public exposure; encrypts some system files |
| Elimination | To get rid of the virus, you should access Safe Mode with Networking (if required) and perform a full system scan with reputable anti-malware. Before that, ensure that the PC is disconnected from a network and a full backup of encrypted files is made |
| System fix | To remediate the system after malware termination, fix the Windows boot, registry, and other feature, use Reimage Reimage Cleaner Intego |
Since the CovidWorldCry ransomware has not been attributed to any threat actor groups, a multitude of distribution methods can be used to deliver malware to the victims. However, security researchers noticed that the primary attack vector is Rig exploit kit, which has been previously used to deliver a variety of other malware, including ransomware like Paradise, Matrix, Sodinokibi, Nemty, Buran and many others.[2]
Some victims that were infected with the CovidWorldCry virus also noticed double encryption performed, which meant that they were hit by a secondary infection – the most prominent ransomware Djvu. This strain is usually proliferated with the help of pirated program installers and software cracks, but it does not mean that the criminal group will not explore additional methods for malware distribution.
Once inside the system, CovidWorldCry ransomware does not proceed with file encryption immediately, as it needs to prepare the machine for the process. In other words, it needs to fully infect it to ensure successful data locking.
Since the malware is distributed mostly via exploit kits, the threat affects those users who have vulnerable software installed on their systems. CovidWorldCry ransomware would deliver an executable file, such as 2020-05-22_17-36-19.exe (which would initiate the infection process), and places it into %AppData%, %Temp%, or another directory. The virus then performs the following changes:
- Deletes Shadow Volume copies with the help of “vssadmin.exe Delete Shadows / All / Quiet” command;
- Manipulates the storage size attributed for Shadow Volume copies;
- Initiates changes within the registry – opens and sets new keys for persistence;
- Terminates processes and starts new ones (LanmanWorkstation and VSS);
- Drops a multitude of malicious files on the system, etc.
CovidWorldCry ransomware is a coronavirus-themed malware that encrypts all personal files on the system and then asks for a ransom payment in Bitcoin
CovidWorldCry ransomware is a coronavirus-themed malware that encrypts all personal files on the system and then asks for a ransom payment in Bitcoin
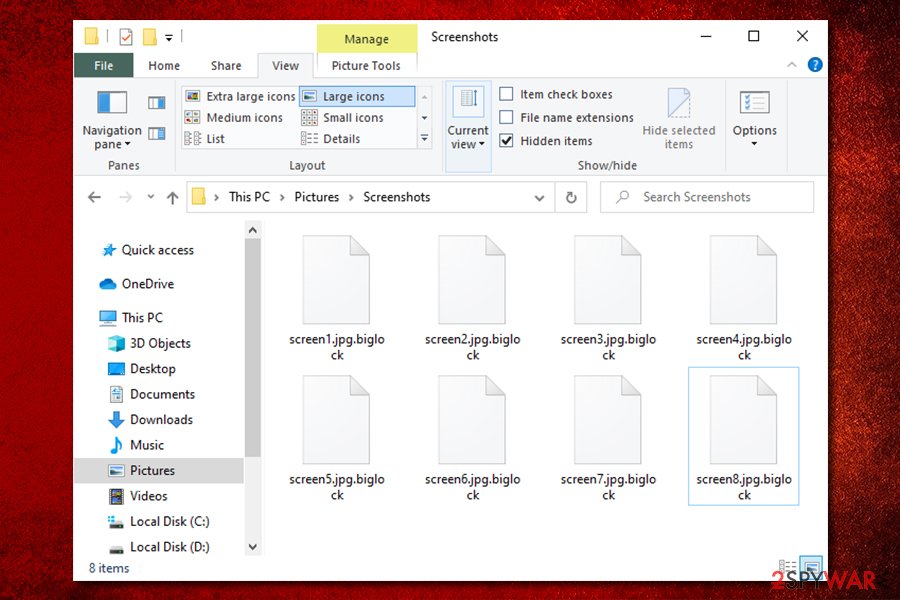
Once the infection process is complete, CovidWorldCry ransomware will look for data to encrypt, which includes PDF, doc, zip, jpg, and many other file types that are most commonly used. Depending on the virus version, files will be appended with either .biglock or .corona-lock extension, and will no longer be accessible to the victims. In addition, the malware will also encrypt some system files, including “ntuser.pol,” or “bootmgr.”
After locking data, threat actors deliver ransom note so that victims would know what happened to their files and what they are supposed to do next. According to them, all data has been locked with ChaCha+ AES, and only they have the required key to unlock it. Unfortunately, this predicament is rather accurate: deciphering the already encrypted files is impossible without the key. However, some other methods can be used (such as third-party tools) in order to retrieve working copies of at least some files after CovidWorldCry ransomware removal.
While the situation is already very difficult for those who did not backup their files regularly, the attackers also claim that they copied all data to their own servers and that they can expose it online or sell it on the dark web:
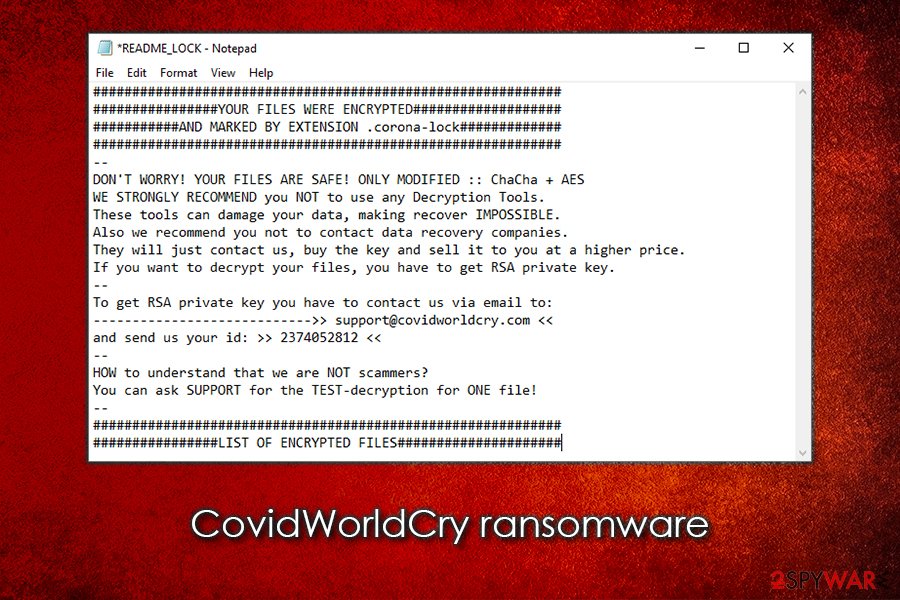
YOUR FILES WERE ENCRYPTED
AND MARKED BY EXTENSION .corona-lock—
DON’T WORRY! YOUR FILES ARE SAFE! ONLY MODIFIED :: ChaCha + AES
WE STRONGLY RECOMMEND you NOT to use any Decryption Tools.
These tools can damage your data, making recover IMPOSSIBLE.
Also we recommend you not to contact data recovery companies.
They will just contact us, buy the key and sell it to you at a higher price.
If you want to decrypt your files, you have to get RSA private key.
—
To get RSA private key you have to contact us via email to:
—————————->> [email protected] <<
and send us your id: >> 2374052812 <<
—
HOW to understand that we are NOT scammers?
You can ask SUPPORT for the TEST-decryption for ONE file!
—LIST OF ENCRYPTED FILES
As evident, CovidWorldCry ransomware infection can be devastating, as users might not only lose their files, money paid for the decryptor, but also have their sensitive information exposed online. Despite this, paying cybercriminals is still not recommended, as the losses can be suffered even after delivering Bitcoins to the attackers.
Instead, you should backup all the files and then remove CovidWorldCry ransomware from the system with the help of reputable anti-malware application. Then, you can follow the instructions we provide below for alternative methods for data recovery. Finally, since the malware modifies Windows heavily, we suggest using Reimage Reimage Cleaner Intego to recover normal functions and fix virus damage.
CovidWorldCry ransomware also encrypts some of the Windows system files, which is unusual for malware of such type
CovidWorldCry ransomware also encrypts some of the Windows system files, which is unusual for malware of such type
Patch the installed software as soon as new updates are out
Software vulnerabilities are types of bugs, otherwise known as flaws, within a program’s code. These are usually found by software developers or independent security researchers. Once found, these flaws are fixed, and a new, improved version of the app is shipped via software updates. Exploit kits allow the vulnerabilities to be exploited, which provides unauthorized access to all the machines that have an outdated application installed (this is also true for the operating system itself).
Rig exploit kit is a relatively old EK that was employed by cybercriminals to inject all types of malware into users’ systems automatically. All they have to do is make users visit a compromised website where Rig is implemented. As soon as the connection is made, a particular payload from a remote server is downloaded and installed automatically, infecting users with ransomware or other malware.
Therefore, it is vital to patch all the installed software on time (especially flawed tools like Adobe Flash, if still used). The best way is to ensure that all the programs are set to be updated automatically. Also, this is just one of many security measures that could protect you from malware infections – practice these precautionary measures provided by experts:[3]
- Employ reputable anti-malware software with real-time protection feature;
- Do not download software cracks or pirated program installers;
- Never allow an attachment acquired from a spam email to run macros;
- Hover the mouse pointer over embedded links inside an email to see the real destination of the hyperlink;
- Use strong passwords for all your accounts and never reuse them;
- Protect your Remote Desktop connection adequately – do not use a default port and use a VPN;
- Employ ad-block, firewall, and other protection features;
- Backup your important files regularly to reduce the impact of ransomware infection.
CovidWorldCry ransomware – learn a correct way to remove
In many cases, users might be shocked after they get infected with the CovidWorldCry virus or another ransomware, as their computers are not the same anymore. None of the valuable files can be opened, and a threatening message from the attackers appears. While cryptomalware infection can be indeed devastating, there is no need to panic, as the outcomes will not change. However, it is important to remove CovidWorldCry ransomware from the system safely.
CovidWorldCry virus appends .corona-lock or .biglock extension to the affected files
CovidWorldCry virus appends .corona-lock or .biglock extension to the affected files
First of all, if you have no backups of your files, you should make a copy of all encrypted data, and only then remove CovidWorldCry ransomware. Otherwise, files might get permanently damaged, and even a working decryptor will fail to retrieve them. Then, perform a full system scan with anti-malware software such as SpyHunter 5Combo Cleaner, Malwarebytes, or a similar tool.
After that, it is up to you whether you want to pay the ransom, although we do not recommend doing so. Sent decryption tools might fail to work, be infected, or you might not receive one at all. Instead, we recommend using third-party solutions that might be able to get at least some .biglock or .corona-lock files back.
This entry was posted on 2020-05-25 at 05:03 and is filed under Ransomware, Viruses.

