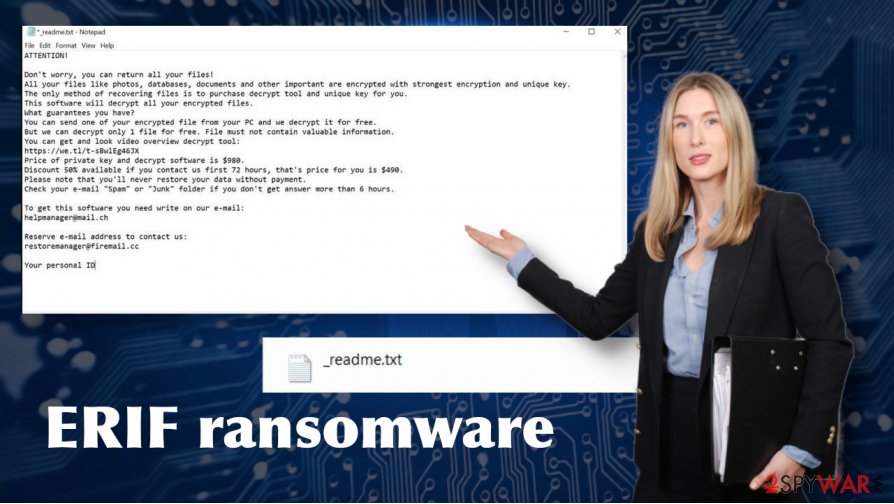
Erif ransomware is a malicious cyber infection that genealogically belongs to the Djvu ransomware family
Erif ransomware is a file-encrypting virus that has started infecting home PC users[1] at the end of July 2020. Cybersecurity experts were quick to confirm the fact that the virus arises from the well-known Djvu ransomware family. It’s the 242nd variant of this infamous cryptomalware, which exhibits more or less the same traits except the novel file extension appended to locked files, which is .erif.
The virus is being most actively distributed via spam email attachments and software license cracks. There’s no way to understand that the attachment or software contains a malicious file because the latter is heavily obfuscated and cannot even be recognized by the AV tools. If the payload dropper is successfully launched, the ransomware scatters malicious .exe and .dll files, launches the PowerShell command to delete Volume Shadow Copies, and alters certain Windows Registry keys, and etc.
However, the mentioned changes are rather invisible. The main symptom of the Erif ransomware infection is inaccessible personal files. All pictures, documents, archives, etc. feature the same .erif file extension, which cannot be removed or changed. Apart from locked files, the victims can see the _readme.txt note on the desktop and non-system folders where they are urged to email ransomware owners via [email protected] or [email protected]. It is clear that the victims are expected to pay $480 ransom in Bitcoins[2] within 72 hours. If later, the price for the decryption key gets doubled. Anyway, Novirus.uk[3] experts do not recommend paying for criminals. Instead, you should rely on alternative .erif decryption methods that we will explain below.
| Name | Erif |
| International classification | Ransomware, a.k.a file-encrypting virus |
| Family | STOP/Djvu ransomware |
| Specificities | Upon infection, the virus drops _readme.txt note for explicit information and locks personal files using the AES-256 encryption algorithm. Consequently, all non-system files get the .erif file marker |
| Contacts | Criminals expect victims to email them via [email protected] or [email protected] |
| Distribution | Djvu ransomware variants are mainly disseminated via spam email attachments and software cracks. However, it may also be distributed via unprotected RDPs |
| Version | 242nd variant of Djvu |
| Decryption | The newest variants of Djvu cannot be decrypted for free. The only official decryption key is stored by the criminals, which cost $490 or $980 in Bitcoins. Nonetheless, victims are advised not to pay the redemption. Instead of that, remove Erif ransomware and take advantage of Data Recovery Pro, Previous Windows version, or similar alternatives |
| Removal | The only way to get rid of the ransomware is to scan the system with a professional anti-virus program |
| IMPORTANT: | Since ransomware directly harms the system, it’s a must to scan the system with Reimage Reimage Cleaner Intego repair tool. Otherwise, corrupted Registry entries, altered system files, and other components can trigger abnormal system behavior |
Erif ransomware is an English-speaking users-targeting virus as its ransom note and other information about the attack is in English only. However, it doesn’t mean that its dissemination is restricted to countries like the US, UK, Australia, and similar. Since this virus is particularly actively spread via software cracks that can be downloaded from Torrent and P2P networks, which are used by millions of people all across the world, any country can become a target.
This cyber threat affects Windows devices only. Erif virus is not adapted to macOS, Linux, or other OS versions. The most vulnerable Windows version is Windows 7, which no longer receives support. Therefore, existing vulnerabilities can be most easily exploited by criminals.
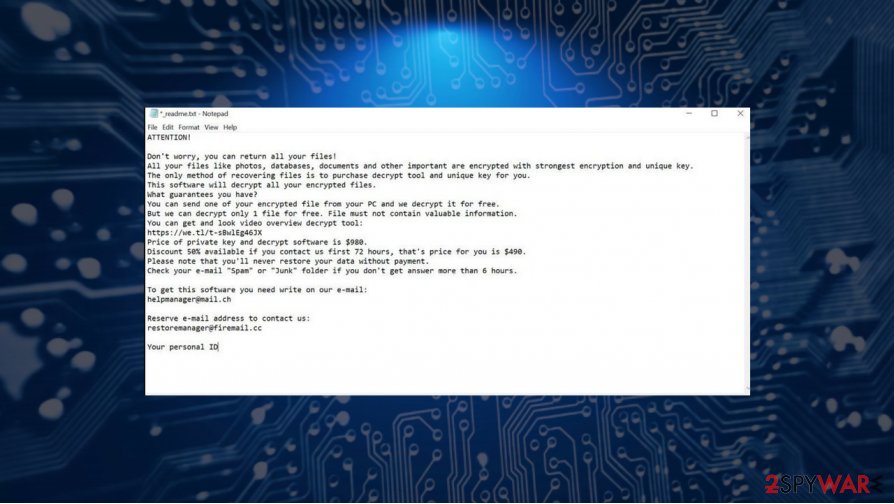
File-encrypting viruses focus on file encryption and victims’ pushing into paying the redemption. Therefore, it’s the main task is to alter as many personal files as possible by appending the .erif file marker as a suffix. However, informing the users in a proper manner is not of less importance. Therefore, the pest creates the _readme.txt note on multiple non-system folders, including Downloads, Temp, Documents, User, etc. The text note contains the following information:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-7YSRbcuaMa
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Your personal ID:
This message is one-sided as the criminals employ a social engineering strategy to scare people into thinking that the only solution is ransom payment. However, as soon as the ransom note is found, we encourage victims to make .erif virus file copies and remove the virus from the system using a robust anti-virus program.
After that, optimize the system using Reimage Reimage Cleaner Intego repair tool to recover normal Windows performance and then try alternative data recovery methods. Please DO NOT fall for downloading free Djvu decryption software. During the research on how to decrypt Djvu variants like Kuus, Maas, Zida, Usam, and others, people end up on shady download sources that provide a free download for the mentioned decryptor. However, it’s yet another trick used by hackers because the free decryptor is the payload of the Zorab ransomware.
Therefore, if you have been infected, do not fall for panic. The first move you have to do is to remove Erif ransomware virus completely. Since it may be rather aggressive and keep its persistence by blocking the security software. However, there’s a workaround solution that Windows provides, i.e. Safe Mode, which automatically disables all necessary processes.
NOTE: Erif removal is not the same as .erif file recovery. Do not confuse these two methods. The elimination of malicious ransomware files and the virus itself requires the usage of professional anti-virus software, which does contribute to the locked files.
Erif virus spreads in a stealthy manner, initiates malicious system changes, and locks personal files to gain easy money
Erif virus spreads in a stealthy manner, initiates malicious system changes, and locks personal files to gain easy money
The Erif decryption is the ultimate step that has to be initiated only after the virus removal. For this purpose, you can either use file backups (if you have cloud storage or external storage for that), download a professional data recovery software, or use in-built Windows features, such as the Previous Version.
Malicious cyber infections take advantage of poor system protection and users’ inexperience
It’s not possible to recognize malicious files injected into emails, software, fake download, and similar medium. This can be done only by professional anti-virus programs. So the main precautionary measure that you can take is the strongest possible security system. Full-featured security package and regularly updated software should ensure the highest, still not hundred-percent, protection from malicious infections.
Do not forget that the main ransomware dissemination technique is spam. Injected with malicious links and attachments, spam emails can be distributed en masses or targeting specific users. Anyway, it’s possible to discern the danger of the email by careful analysis of its sender, main body text, grammar, type, and similar traits. Besides, you can always use the email scan feature that most of the professional AV tools offer.
Another measure that would help to stay away from malicious cyber infections is related to pirated software. Hackers frequently take advantage of cracks and keygens that millions of people keep downloading to avoid paying for the license of software like Windows, Adobe Acrobat, Photoshop, and many others. Unfortunately, there’s no way to check the pirated software or its files. Thus, we strongly recommend you to stop using illegal software not only because you infringe the copyright law, but because you risk being infected by a malicious cyber infection.
Crooks may try to trick users into downloading maliciousE Erif decryptor for free. Do not fall for the trick because it’s yet another ransomware
Crooks may try to trick users into downloading maliciousE Erif decryptor for free. Do not fall for the trick because it’s yet another ransomware
Delete Erif ransomware along with its malicious files to recover system’s performance
Erif virus is activated as soon as the potential victim accidentally enables the payload dropper. As we have already explained, the latter can be disguised within spam email attachments, pirated software, or injected manually by targeted brute-force attacks. Anyway, the damage is as big – personal files locked, the system compromised.
One of the most important things is not to fall for panic. The first thing to perform – a full Erif virus removal using robust anti-virus tools, such as SpyHunter 5Combo Cleaner or Malwarebytes. Reboot the system into Safe Mode (the tutorial below) and launch the AV scanner. The scan process may take some time, so be patient and let the software do the trick.
Once the virus is quarantined and removed successfully, we recommend employing a reliable system repair tool and using it for fixing virus damage. It’s a tool oriented to Windows optimization, recovery of damaged system files, registry check, and similar tasks. Once you remove Erif virus and recover the system, keep going with the file recovery methods.
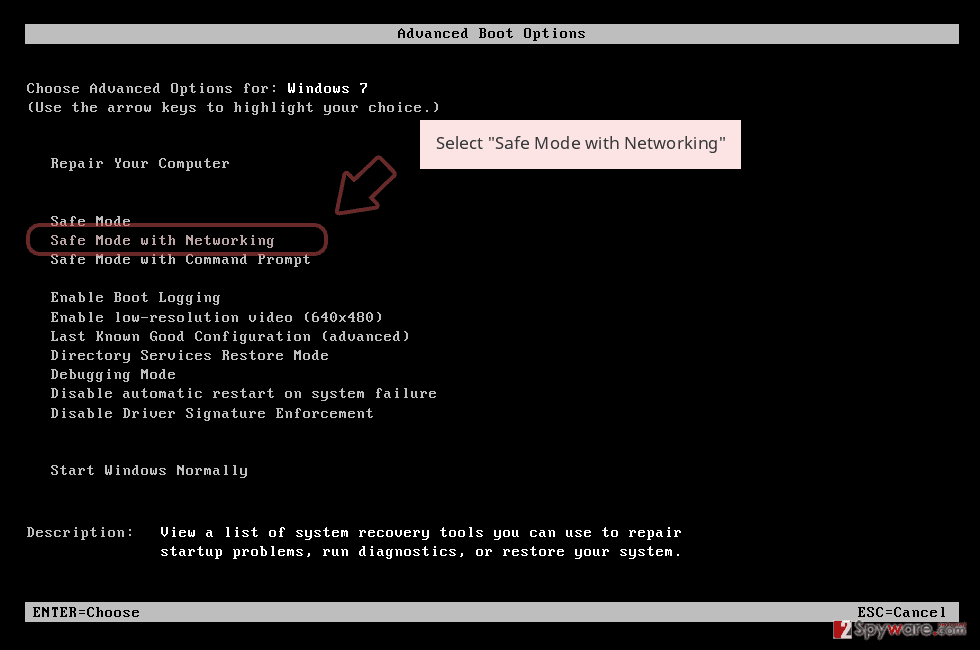
Remove Erif using Safe Mode with Networking
The guide below helps users to reboot Windows into Safe Mode with Networking if they haven’t done this procedure before:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
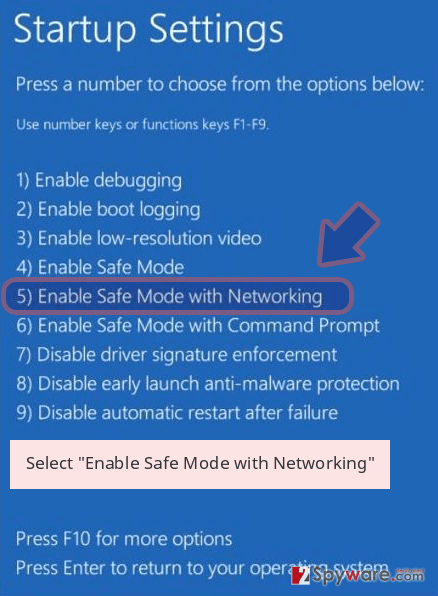
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Erif removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Erif using System Restore
Enable previous Windows Version to recover damaged system files.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Erif from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
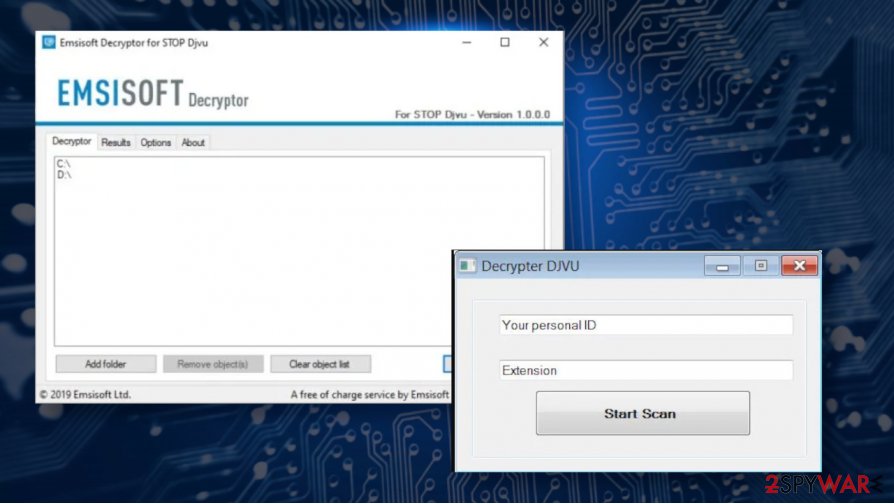
Unfortunately, a free Erif decryption tool is not available. The virus takes advantage of the unique online keys for every victim, the latest Djvu variants (launched after August 2019) cannot be decrypted for free. The older variants (some of which are still active) can be deciphered using a free STOP/Djvu decrypter. Otherwise, you should rely on alternative methods, some of which are listed below:
If your files are encrypted by Erif, you can use several methods to restore them:
Employ Data Recovery Pro
This robust data recovery application can help to retrieve files after the Windows crash, as well as a ransomware attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Erif ransomware;
- Restore them.
Windows Previous Versions is the file recovery feature
When you enable System Restore, you can rely on Windows Previous Versions and restore those encoded files yourself. Please note that this process requires much time because files can be recovered on-by-one only.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
No Erif decryptor available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Erif and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
The government has many issues in regards to tracking users’ data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Computer users can suffer various losses due to cyber infections or their own faulty doings. Software issues created by malware or direct data loss due to encryption can lead to problems with your device or permanent damage. When you have proper up-to-date backups, you can easily recover after such an incident and get back to work.
It is crucial to create updates to your backups after any changes on the device, so you can get back to the point you were working on when malware changes anything or issues with the device causes data or performance corruption. Rely on such behavior and make file backup your daily or weekly habit.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware occurs out of nowhere. Use Data Recovery Pro for the system restoring purpose.
This entry was posted on 2020-07-24 at 04:53 and is filed under Ransomware, Viruses.

