Kronos malware is the trojan designed to steal sensitive information from victims and transfer funds from the bank accounts
 Kronos malware – banking trojan that had a few updates since 2014 when it first got released. This malware is the type of virus that pretends to be a simple email attachment, so it can infect the computer further and spread other malware. It can infect the machine and give the particular attacker remote access to financial details, emails or passwords and logins. Trojan also has this web injecting functionality that helps directly record credentials from fake financial pages. It first was spotted in 2014 when in the Russian underground forum where the virus got offered for $7,000. Developers claimed various detection evading modules and other features to make more sales. This was a tool that got used to stealing sensitive details like banking data directly from users machines with the help of keyloggers
Kronos malware – banking trojan that had a few updates since 2014 when it first got released. This malware is the type of virus that pretends to be a simple email attachment, so it can infect the computer further and spread other malware. It can infect the machine and give the particular attacker remote access to financial details, emails or passwords and logins. Trojan also has this web injecting functionality that helps directly record credentials from fake financial pages. It first was spotted in 2014 when in the Russian underground forum where the virus got offered for $7,000. Developers claimed various detection evading modules and other features to make more sales. This was a tool that got used to stealing sensitive details like banking data directly from users machines with the help of keyloggers
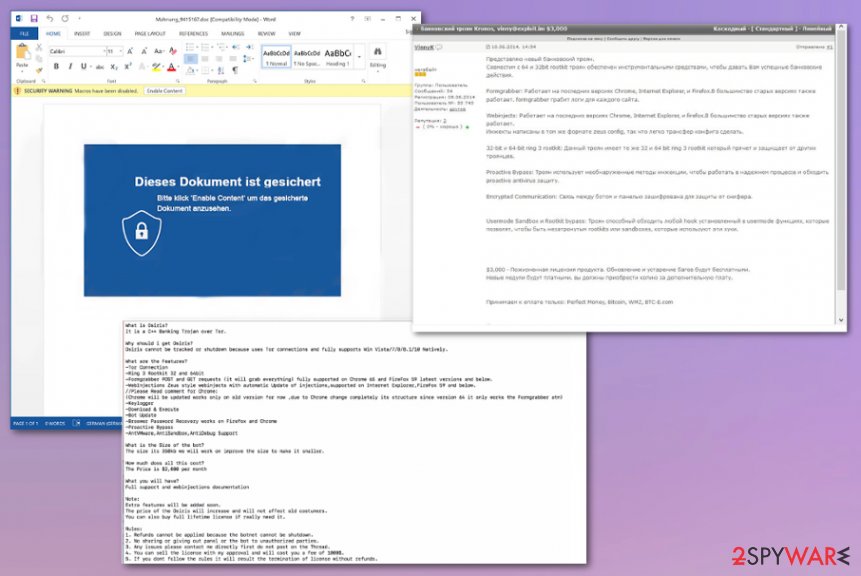
This high-risk trojan is sent via spam emails that come to thousands of people every day. Once the email attachments get opened and user downloads or enable the content, Kronos ends up installed on the machine without causing many symptoms at this point. Most of the trojan infections got detected in Poland, Germany, and Japan, but campaigns are not that specifically targetted, so anyone anywhere can end up with this threat on their machine. Many researchers thought it was no longer active after the first campaign in 2014, but it came back a few times after that.
| Name | Kronos malware |
|---|---|
| Type | Banking trojan/ info-stealer[1] |
| Tactics | A trojan is set to infiltrate the system without any particular symptoms and steal credentials, banking site logins and passwords or redirect the person from an email to malicious URL of a banking site that is injected with malicious code, so all the details filled out get collected |
| Distribution | Emails with infected attachments, injected with macro viruses and malicious online pages deliver this malware. Pirated software, cracks and game cheats also can help distribute the threat. As well as other infections |
| Danger | The trojan is aiming to steal credentials of banking accounts, so transfers, purchases could be made in the name of the person. This is how many people get into debts and lose their funds, savings. More personal credentials can be used in targeted scam campaigns later on |
| Known since | 2014 |
| Elimination | To remove Kronos malware, you need a good anti-malware tool that could detect the threat and clean the machine from all the traces |
| Repair | Malware can run in the background without notice and change additional settings, disable functions to keep the persistence, so check your machine with a proper PC repair tool like Reimage Reimage Cleaner to make sure that virus damage is fixed |
Kronos malware is based on a man-in-the-browser technique that helps trojan to record needed information. The method allows to exploit vulnerabilities to modify the content on the web browser, so any sensitive information like credentials and logins can get collected once entered. Trojan targets finance related sites because criminals aim to get as much revenue as possible using hacked accounts and performing financial tasks, purchases, transfers. This is how people lose their money, savings or even get into debt when criminals use their accounts to profit.
Kronos malware was spotted in a few different instances and after the first campaigns, it was thought that trojan is no longer active and working. However, it came back with a new command-and-control feature that works wit Tor anonymizing network.
These were the campaigns mainly targeting Germany, Poland, and Japan.[2] During analysis on these newer campaigns researchers also identified that Kronos malware may have been renewed and rebranded with the name Osiris. A trojan is being sold on underground forums and other market places with this name.
Kronos malware, first discovered in 2014 reportedly has four distinct campaigns distributing malicious files that lead to direct trojan installation. A trojan is capable of stealing information from banking websites. It also includes Ring3 rootkit that helps to defend from other trojans. In 2016, when trojan was no longer found active, researches believed that malware was no longer working.
Kronos virus came back in 2017 when the FBI accused a whitehat hacker who stopped WannaCry for building the trojan.[3] Hutchins was named a hero when he discovered a kill switch for the WannCry ransomware and stopped the infamous virus. FBI claimed that Kronos banking trojan has been around since June 2014 and began as a banking trojan based on the Zeus virus code. 
Kronos malware is the threat that releases spam email campaigns with macro-infected documents.
Differences and similarities of Kronos malware campaigns
In Germany, the recent malware campaign was spread using spam emails with claims that notifications are sent from financial firms. Subject lines of such emails stated about terms and conditions, updates of the privacy policy. Kronos malware used URLs connected to command and control servers and documents containing macros that get triggered when the Word document gets opened and additional content enabled by the user.
One of the emails used in Germany-targeting Kronos virus campaigns:
Subject: Aktualisierung unsere AGBs
Sehr geehrter Herr Max Mustermann,
Die Fidor Bank optimiert ihr Angebot permanent weiter, um Sie noch besser bei Ihren Finanzgeschäften zu unterstützen.
Daher werden wir ab dem 07.07.2018 folgende Neuerungen/Anpassungen einführen:-Ausbaut des Zahlungsverkehrs in Bezug auf Überweisungen sowie Sonderbedingungen hinsichtlich der Einführung des
Produktes „Geld Notruf“-Anpassung unserer AGB nach §22-31 DSGVO, zur Rechtsgrundlagen der Verarbeitung personenbezogener Daten
Der anschließend kurze Datenabgleich ist erforderlich um Sie als primären Kontoinhaber zu legitimieren. Sollten wir unregelmäßigkeiten bei Ihrem Datenabgleich feststellen, ist die Bestätigung unserer angepassten AGBs nurnoch auf dem Postweg möglich,
und notwendig um die Handlungsfähigkeit Ihres Kontos zur erhalten.Legitimation beginnen
Wichtiger Hinweis:
Die geänderten AGB gelten als von Ihnen angenommen, wenn Sie den Datenabgleich erfolgreich durchgeführt haben, und Sie der Änderung nicht innerhalb von sechs Wochen schriftlich widersprechen.
Sofern Sie Fidor zu den geänderten Bedingungen nicht weiter nutzen möchten, senden Sie Ihren Wiederruf bitte an: Fidor Bank AG, Kundenservice Widerruf, Sandstr. 33,
D-80335 MünchenSie haben noch Fragen? Unser Kundenservice steht Ihnen jederzeit zur Verfügung.
Mit freundlichen Grüßen
Ihr Fidor Bank Team
Attacks in Japan were discovered on July 15-16. The malvertising-based campaign involved chain emails with URLs redirecting to sites with malicious JavaScript injections. The RIG exploit kit was also included and smoke-loader downloader malware led to Kronos banking trojan drop.
The same attackers targeted Poland on the same days of July 2017. In this campaign., criminals used attachments resembling invoice attachments with malicious code to exploit the Microsoft Equation Editor vulnerability also known as CVE-2017-11882 that got patched the same year.[4]
The fourth campaign of the trojan was observed using the English language and music streaming website, in particular, to lure victims. All of the versions observed uses the same Windows API hashing technique and hashes, same C&C protocol and encryption and the code that is identified as Kronos by the developers themselves. A few newer versions also adopt key-logger functionalities and more similarities to the Zeus Panda banking trojan and the original Zeus web-injecting feature.
These facts and associations with other malicious programs make it more dangerous and persistent. Nevertheless, if you noticed any suspicious activities with your computer try to scan the machine using the AV tool and remove Kronos malware as soon as possible. Contact your provider when unauthorized transfers appear on your account activities.
Kronos malware removal may seem impossible since there is no particular program that trojan installs on the machine, but anti-malware tools based on detecting malicious behavior can find and terminate files and programs related to this trojan, its own payload dropped on the computer. You need to trust a reliable program and fully scan the machine, so it can eliminate the malware. Also, we recommend getting a system optimizer or a repair tool that could find and fix virus damage in crucial system parts and folders after the infection cleaning. Rely on Reimage Reimage Cleaner . 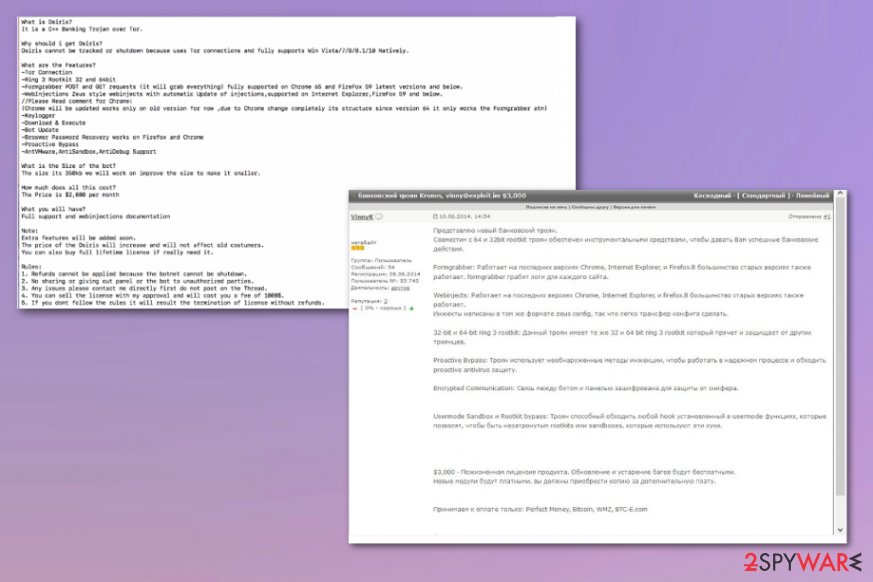
Kronos malware is the threat that poses as financial companies, so people will open malicious email attachments.
The more dangerous the virus, the more stealthily the spreading technique
Trojans, worms, ransomware, and other viruses that end up installed directly on the machine cannot be easily noticed and spotted during the infection because criminals use deceptive methods and misleading techniques to hide their purposes of dropping the threat. In most cases, such information-stealing trojans and banking malware get delivered via spam email campaigns where subject lines state about important information and the sender resembles a company or a service that people know.
Such emails contain messages and URLs or Microsft document attachments containing encouragements to enable the content or allow the macros. Once the malicious files get permission to download the code, the machine gets infected and affected by the trojan directly, so all the processes can get triggered.
Often malicious actors can inject web code on legitimate-looking financial sites, so all the information entered there end up collected by criminals. These hyperlinks also are offered on those emails, so stay away from any suspicious emails and notifications you are not expected to receive.
Make sure to terminate Kronos malware virus and clean the machine to avoid money and data loss
When you notice any suspicious activity on the machine and think that your device may be affected by the virus, you should scan the system immediately and use a reliable anti-malware program for that, so you can remove Kronos malware or any other virus if needed. When the software indicates all the detections follow suggested steps and clean the machine.
It may be difficult to perform Kronos malware removal when the trojan alters particular functions, disables programs or changes settings, so reboot the machine in a Safe Mode and then run SpyHunter 5Combo Cleaner or Malwarebytes o get rid fo the virus. Then you should fix those unwanted changes and virus damage with a program like Reimage Reimage Cleaner , for example.
This entry was posted on 2020-01-28 at 05:08 and is filed under Trojans, Viruses.

