Masodas ransomware is a crypto virus that adds the .masodas file extension to all encrypted files and offers a discount for the ransom
Masodas malware – ransomware that uses AES or another encryption ciphers for file locking process
Masodas malware – ransomware that uses AES or another encryption ciphers for file locking process
Masodas ransomware is a file locking virus that enters the machine after victims open a malicious spam email attachment, download pirated software, fail to update the operating system on time, use weak RDP protection,[1], etc. Soon after the infiltration, the malware makes use of AES or another powerful encryption algorithm to lock pictures, videos, databases, documents, and other files. Once that is done, .masodas gets on every affected file, hence the name of the intruder.
The encryption process is focusing on your data because once files are encrypted, _readme.txt file shows up on your desktop and gets added to every folder containing locked files. The note reveals contact information and informs about possible steps further. However, although criminals claim the only solution is to pay, we don’t recommend doing so. There are other solutions for Masodas ransomware attack and you can recover, at least some of your files without paying.
Although users say that decryption tools are not recovering all of their files, the STOP decryption tool should be the best option for you. Yes, it is not magical and can only restore data encoded using offline keys, but it is the only solution as of right now. You can store files related to the virus and use them later once there are more decryption options or tools especially for Masodas gets released.
| Name | Masodas |
| Type | Ransomware |
| Ransomware family | STOP/Djvu is the family that this virus comes from. Due to this relation, you shouldn’t trust developers with your files |
| Distribution | Spam emails, exploits, weak RDP connections, fake updates, web injects, etc – common vectors for file-locking malware distribution. Masodas payload is more known for being included as an installer for cracks, cheats and illegal copies of software provided on torrent sites |
| File extension | .masodas gets added at the end of every file encrypted by this virus. This indicates which files cannot be opened and used |
| Ransom note | _readme.txt – a file that reveals all the needed details about the ransomware attack |
| Contact | [email protected] or [email protected] |
| File decryption | STOPDecrypter [download link] and third-party recovery software might help; otherwise, files can only be replaced with your backups |
| Termination | You should remove Masodas ransomware by using security software or anti-malware like Reimage Reimage Cleaner Intego. You need to clean the system before any file recovery, to avoid permanent damage and data loss |
This version of Djvu ransomware came out during the most active month for this virus developers because in these few weeks criminals revealed more than 30 new variants. Not much changed from one another but all dangerous and damaging. Since the main researcher Micael Gillespie is analyzing these versions and updating the decryption tool, at first, you may need to wait for the decryption possibility. However, some users[2] stated that there are more issues regarding this version.
Masodas ransomware targets the most common files that can be found on a regular computer system, such as .jpg, .mpg, .html, .xls, .mp3, .zip, .db, .doc, etc. after the encryption, the files are converted into the following: [file_name].[file_extension].masodas. Thus, a picture.jpg is turned into picture.jpg.masodas, and files modified in such a way can no longer be opened and no data can be extracted.
Additionally, Masodas ransomware changes the way Windows operates by altering the Windows registry, and other alternations to perform the encryption process without interruption. After that, all the personal data is marked with .masodas extension and is no longer accessible to users.
Masodas virus also places a ransom note _readme.txt in order to provide users with information – they are asked to contact hackers via the [email protected] or [email protected] and then pay $980 or $490 ransom in Bitcoin to retrieve the data. Masodas ransomware belongs to STOP/Djvu family, so experts recommend avoiding cybercriminals, and instead of trying alternative data recovery solutions, including using the STOPDecrypter tool. 
Masodas virus – ransomware that can come delivered through malicious executables, p2p sites, fake updates, etc.
Masodas virus – ransomware that can come delivered through malicious executables, p2p sites, fake updates, etc.
It is worth noting that the data encrypted by Masodas virus is not corrupted – it is merely locked by a unique key that resides on a remote server only accessible for hackers. That what makes ransomware viruses so dangerous, as much of valuable data might be lost simply because the victim is unable to pay the required ransom. Nevertheless, Masodas ransomware removal should be the top priority, and paying the ransom is not recommended in the first place.
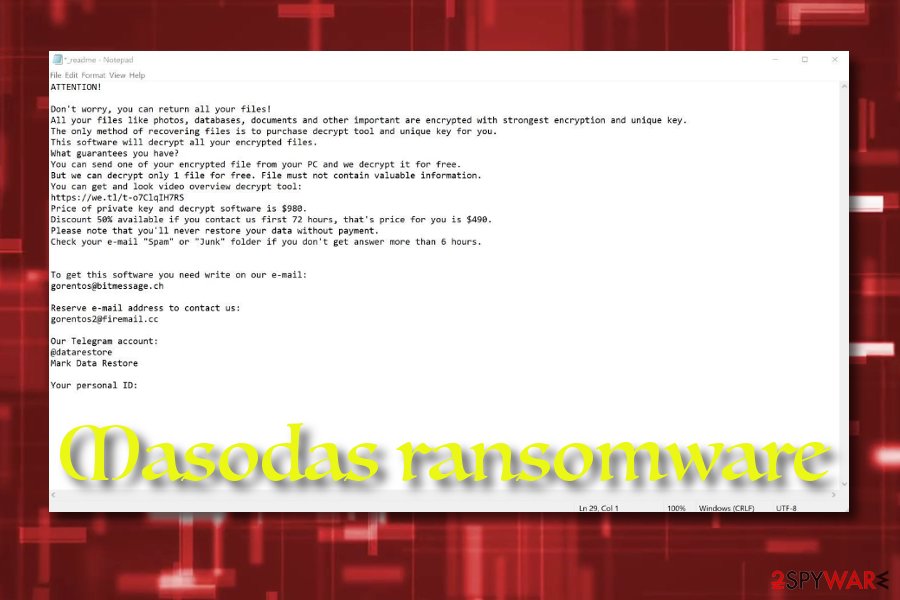
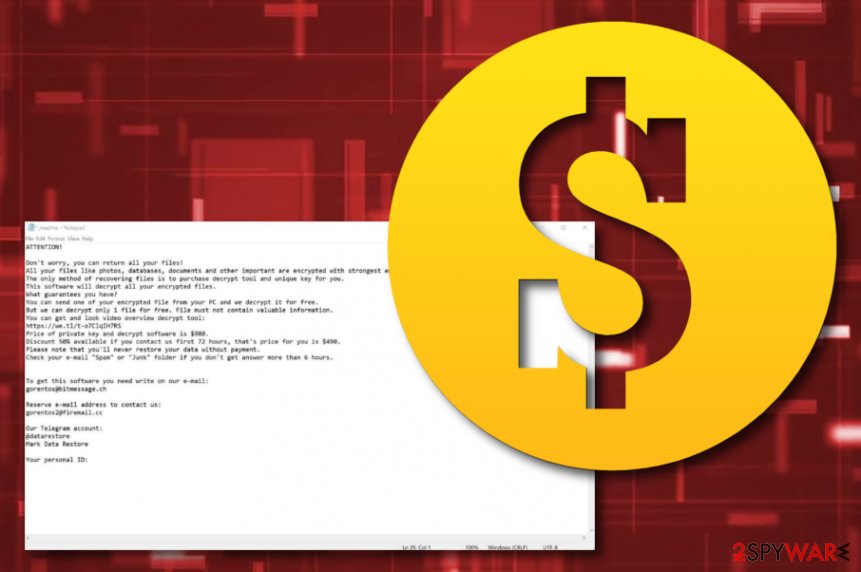
To convince users to pay the demanded ransom in Bitcoin, hackers even offer a 50% discount in the ransom message that reads:
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-o7ClqIH7RS
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]
Decryption possibilities
Even if you can afford the ransom or the discount is attractive to you, keep in mind that Masodas ransomware authors might never send you the required decryption tool, so you will end up losing your money along with the personal data. Thus, instead, remove Masodas ransomware using security software like Reimage Reimage Cleaner Intego and then proceed with alternative file recovery solutions.
For that, you can either employ a specific tool – STOPDecrypter, which might work if the encryption process was performed when your computer was offline or the malware was unable to contact the C&C server.[3] Alternatively, you might try to employ third-party recovery solutions, although the chances of them working are relatively slim. If that does not work, the only choice is to make a copy of the .masodas files and wait till a working tool is released.
The first step that you should go for once infected with ransomware is disabling any optimization tools or security software yourself because those programs can remove crucial files of the virus that may be needed for file recovery. Of course, you need to run an anti-malware tool to remove the traces, but store various data of the ransomware on your external device, so it can be used later on.
For available decryption tools you can check:
However, some of the samples show that Masodas includes a unique patch that is disabling STOP decrypter and other tools. Also, this service cannot help with data encoded using online keys, so you are not able to get your files back. There are many other versions released after this one with changed encryption methods entirely, so if you encounter the updated Masodas or a newer variant from this family on the machine, there are solutions for you. Read the forum to know.
Ransomware hiding places throughout the Web sphere
Internet security experts from NoVirus.uk[4] state that the most popular ransomware distribution source is email spam. Criminals attach the malicious payload in the form of an executable, word document, or zip file. Also, the malware might come inserted into a particular hyperlink inside in the message body.
Ransomware viruses and other malware can come injected into bogus hyperlinks and adverts on unprotected networks such as peer-to-peer ones, online-gaming, streaming, gambling, and similar ones. Also, malicious apps might be disguised as fake software updates or handy products.
These are common ways of ransomware distribution, but it is known that this family spreads via pirated files like game cheats, software cracks or serial numbers to some security tools, legitimate license keys. Sony Vegas, Adobe tools or video game serial numbers and cheats downloaded from torrent pages are known as the ones that previously delivered malware.
Don’t trust such sites and services, even though the torrent has many satisfied receivers, seeders or the account is “verified”. You cannot know the particular source where those files are coming from, so stay away from illegal activities if you wan to keep the machine virus-free.
Remove Masodas ransomware from your system immediately
There are plenty of users who might wonder whether to pay the ransom for Masodas ransomware virus authors. While we highly discourage it, those who do not see another choice might want to risk it, although it is unknown if file decryption will be successful.
Nevertheless, you should rather remove Masodas ransomware first and then apply alternative recovery solutions. The best tools are anti-malware programs like Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner, or Malwarebytes that can detect and remove malware, PUPs, or even fix damaged files on some Windows devices.
For complete Masodas ransomware removal, you should enter Safe Mode with Networking, as malware might interfere with the operation of the security application. Once inside, perform a full system scan – it will ensure that all the malicious components of the ransomware are gone. Please check the instructions below for the termination process and guidelines on how to attempt file recovery below.
This entry was posted on 2020-06-04 at 11:12 and is filed under Ransomware, Viruses.

