Mpaj ransomware – file locking malware that belongs to the notorious Djvu virus family
Mpaj ransomware is a data locking malware that is mainly spread via software cracks
Mpaj ransomware is a data locking malware that is mainly spread via software cracks
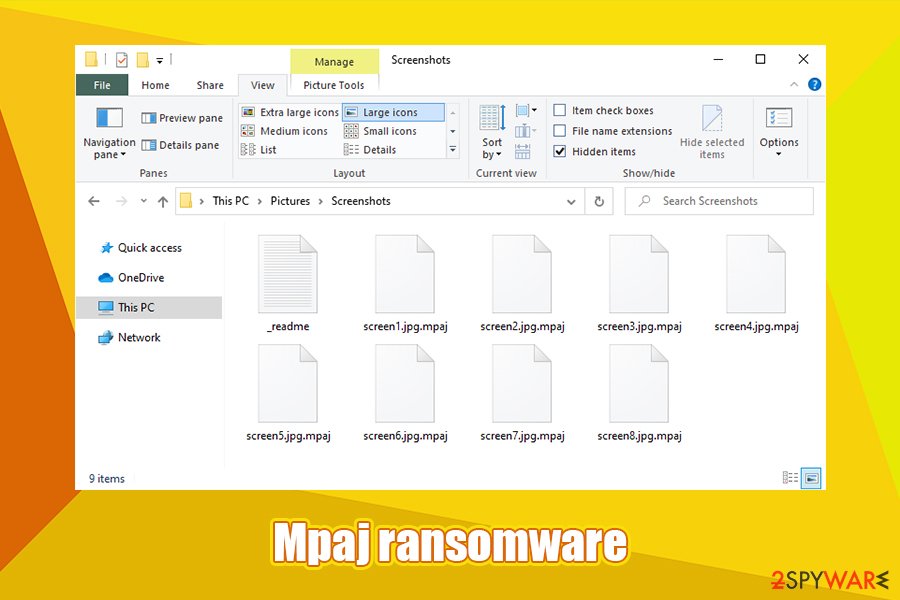
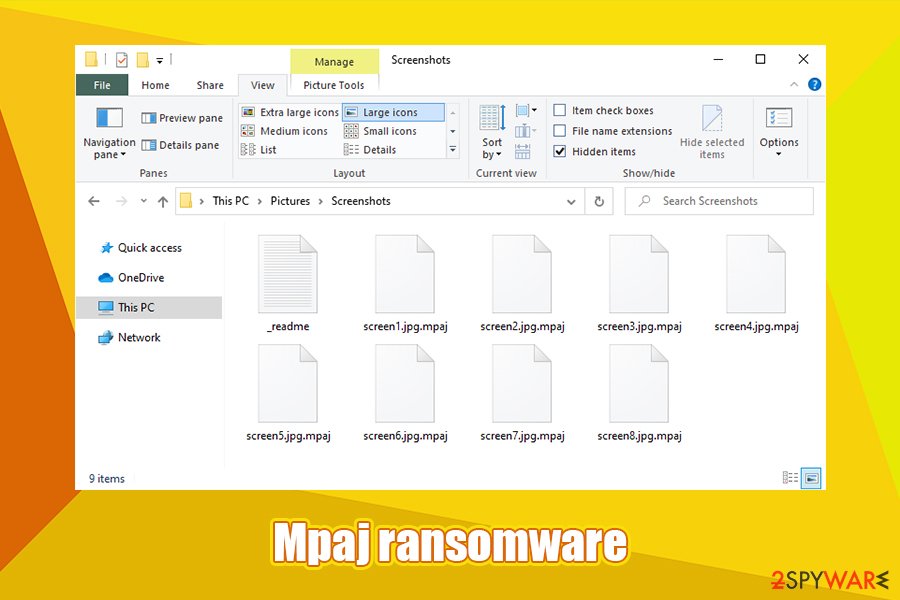
Mpaj ransomware is a data locker that was first spotted attacking users worldwide in early April of 2020 and is a part of a large malware family Djvu. The virus encrypts documents, databases, pictures, videos, and other data on a compromised computer using asymmetric RSA cipher,[1] appending .mpaj extension in the process. Suchlike modified files can no longer be opened, and victims require a specific decryption software available only from Mpaj ransomware authors.
After the data locking process, the Mpaj virus delivers a ransom note on the desktop and most of the folders – _readme.txt. According to threat actors, only they can provide the required decryption software in order to recover locked files, and they are not giving it away for free. Victims are asked to pay $490 in Bitcoin for the decryptor, but first, they have to email criminals via [email protected] or [email protected] emails for negotiation purposes. In case the demands are not met within 72 hours after the infection, the cost of the tool doubles to $980. Nonetheless, users are encouraged not to contact criminals or pay for the ransom, as they should first focus on Mpaj ransomware removal and alternative data recovery methods.
| Name | Mpaj ransomware |
| Type | File locking virus, cryptomalware |
| Family | Malware is a variant of the STOP/Djvu virus family |
| Infiltration | 99% of the time, this malware strain is delivered via pirated software installers and software cracks, keygens, loaders, and similar tools which are downloaded from insecure third-party sites (such as P2P) |
| Encryption method | RSA is applied to lock all non-system files on the machine |
| File extension | Personal files like pictures, videos, MS Office documents and similar data is appended with .mpaj marker |
| Ransom note | _readme.txt is delivered to users’ desktops, as well as each of the folders where locked files are located |
| Contact | Crooks ask to email them via [email protected] or [email protected] |
| Ransom size | If the ransom is paid within 72 hours of infection, it will cost victims $490, although this sum doubles to $980 later |
| File recovery |
The safest way to recover data is to use backups. If none are available, these are the alternative options:
|
| Malware removal | Use reputable anti-malware software like SpyHunter 5Combo Cleaner or Malwarebytes and perform a full system scan |
| System fix | To fix Windows after a malware attack, you should employ repair tools like Reimage Reimage Cleaner Intego |
Mpaj ransomware is one of the versions of a well-known family – Djvu, which was first discovered back in 2017. Since then, more than 200 variants were released, previous ones being Foop, Mado, Mool, and many others. Prior to August 2019, the malware was using a less secure encryption method, which allowed security researchers to deliver tools like STOPDecrypter – it returned access to users’ files for free, in some cases.
However, cybercriminals are sophisticated individuals (especially those that operate such an extensive malware strain like Djvu), and they soon realized that they need to do something to stop victims from recovering their data for free. Therefore, since August 2019, threat actors began using the asymmetric encryption algorithm RSA, fixing encryption bugs in previous versions.
Nonetheless, Emsisoft managed to release a new decryptor that works for all versions that use AES encryption, and also for later variants that use an offline ID to encrypt data, and Mpaj ransomware is one of them. Thus, experts advise users not to pay the ransom and hope that the Mpaj virus failed to contact its Command and Control server[2] during an encryption period.
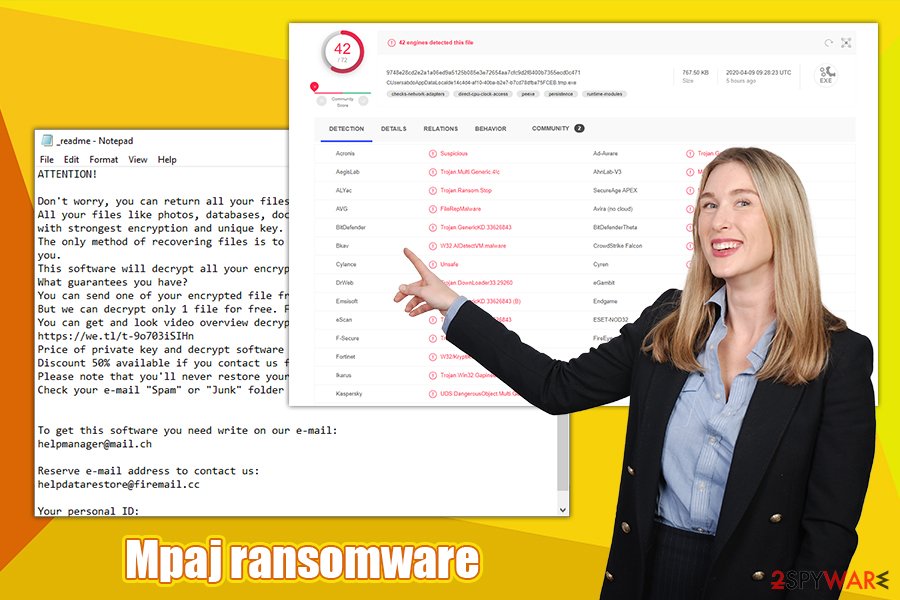
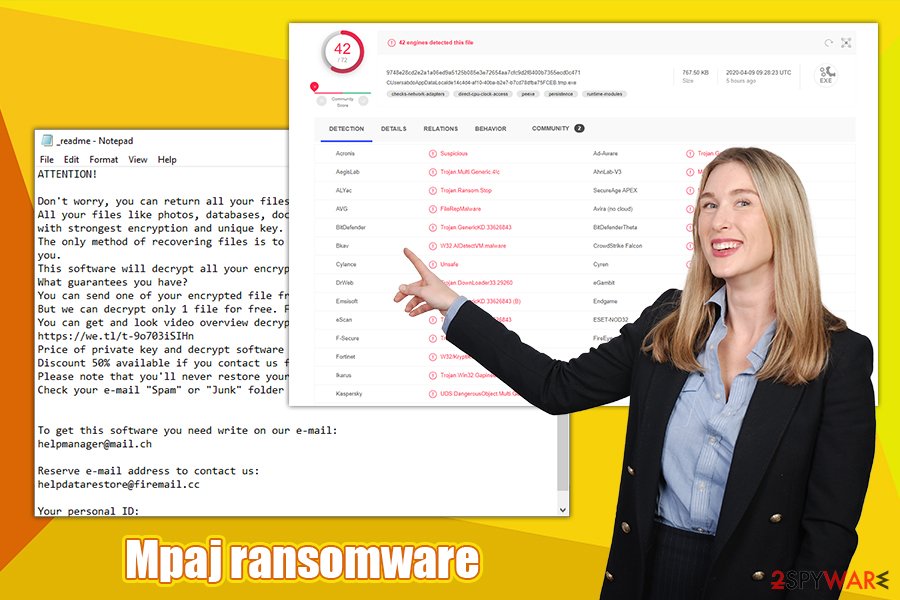
If you have backups, you can simply remove Mpaj ransomware without giving too much thought to it. If you do not have a working copy of your files, you should first backup the encrypted ones before you get rid of malware from your machine. You can perform a complete Mpaj ransomware removal with the help of comprehensive anti-malware software. Note that security tools can also protect you from a malware attack; for example, these vendors detect the malicious executable under the following names:[3]
- FileRepMalware
- Win32.Trojan-Ransom.STOP.09RWCU
- ML.Attribute.HighConfidence
- Ransom:Win32/STOP.BS!MTB
- UDS:DangerousObject.Multi.Generic
- Trojan.DownLoader33.29260, etc.
Developers of Mpaj file virus use a seemingly primitive, yet effective way to deliver malware to as many users as possible – software cracks and pirated software installers. These tools can usually be found on insecure torrent or similar sites that host them. As soon as the malicious file, that can be named as anything, is executed, the infection routine begins.
Mpaj ransomware is a cryptolocker that might prevent users from accessing security-related sites and harvest sensitive information
Mpaj ransomware is a cryptolocker that might prevent users from accessing security-related sites and harvest sensitive information
To ensure a successful encryption, Mpaj ransomware first performs a variety of changes to Windows operating systems, which include modifications to the registry, shadow volume copy deletion, disable of startup repair function, communication establishment, and much more.
Besides making these changes, Mpaj ransomware virus can also deliver additional functionality that is not beneficial to the user in any way. Previous Djvu versions were observed being delivered along with other malware, such as data stealer AZORult. Also, it inserts an additional module that can harvest information from users’ web browsers and prevent them from visiting security themed sites (by modifying Windows “hosts” file).
Upon execution of these changes, Mpaj ransomware begins to look for files to encrypt, and targets the most popular extensions like .jpg, .doc, .pdf, .odt, .txt, .zip, .log, .xls, and many more. After the relevant data is found, the virus starts encryption process, during which it displays a fake Windows Update pop-up to prevent any disruptions. It is important to note that the data does not get damaged – it is simply locked with a unique identifier which is only accessible to the attackers. This is one of the main reasons why Mpaj ransomware along with other strains became the to-go malware for money extortion purposes.
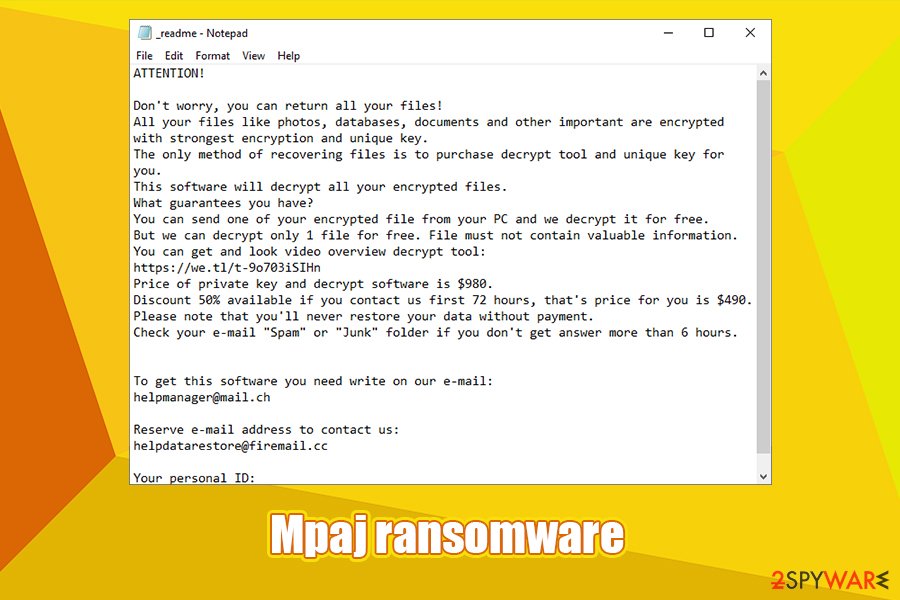
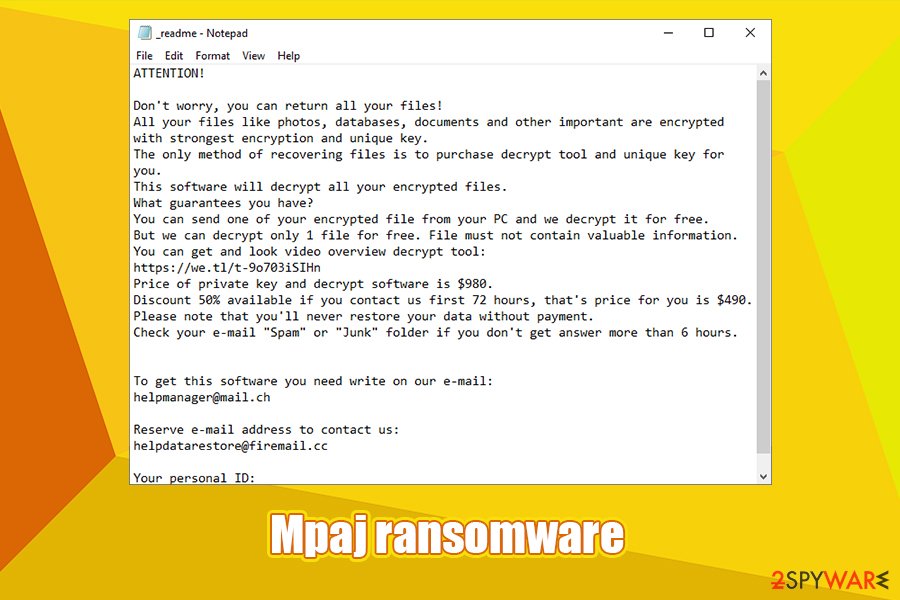
To ensure that victims get the memo and know what to do next, Mpaj ransomware drops a ransom note _readme.txt, which reads:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-9o703iSIHn
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Your personal ID:
The ransom note is virtually identical to all the previous notes that were used by this malware, and, typically, only the contact details differ from one version to another. Nevertheless, as previously mentioned, you should consider paying the ransom as an absolute last resort, as it only profits the attackers and funds their illegal business. Besides, there is also a chance that the Mpaj decryptor will not be delivered to you in the first place, as hackers can simply ignore you after you pay.
Thus, first try to use alternative decryption methods we provide below, as you might be one of the lucky few whose files were encrypted with an offline ID. After you get rid of malware, do not forget fix damage done to the system files with the help of such tools like Reimage Reimage Cleaner Intego.
Once Mpaj ransomware encrypts data, recovering it without backups is difficult
Once Mpaj ransomware encrypts data, recovering it without backups is difficult
Avoid ransomware infections in the future
Most likely, everybody knows that pirating software and using cracks come with great cybersecurity risks, although many tend to ignore threats and simply continue what they were doing. If you are one of those people, you should stop using software cracks immediately, as it is not only illegal but can also result in a loss of access to personal files, possibly, permanently.
Software cracks are relatively unique executables since they are designed to break a code within other software and bypass the licensing process so that the app can be used for free. Due to this functionality, almost all security applications will flag a crack as malicious, regardless if it includes malware code inside of it. Therefore, there is no effective way to verify if the tool is actually malicious (at least not for regular computer users). The best piece of advice would be to stop downloading pirated software and cracks altogether.
Additionally, there are other essential measures that should be practiced when trying not to infect the computer with malware, and that involves equipping it with advanced security software, backing the most important files, never opening attachments of suspicious emails, browsing cautiously, etc.
Backup encrypted files before terminating Mpaj ransomware
As previously mentioned, in case Mpaj ransomware removal is performed too soon or third-party tools employed before its elimination, it might result in a complete data compromise, and not even a working decryptor would be able to help you after that. Therefore, if you have no backups, make sure you put the most important files to you into an external or virtual drive before doing anything else.
Once you copy all your data, you can remove Mpaj ransomware from your system using anti-malware, although keep in mind that advanced malware might tamper with security software. In such a case, you should bypass this functionality by accessing Safe Mode with Networking – we provide the instructions for that below. Only after you are sure that the Mpaj virus, along with any other malware, is gone, you should proceed with the recovery guide listed below.
Additionally, you should access the following location and delete Windows “hosts” file in order to access security-related sites without restrictions:
C:\Windows\System32\drivers\etc\
This entry was posted on 2020-04-09 at 10:14 and is filed under Ransomware, Viruses.

