Nomikon ransomware – a file-encrypting threat that uses the mixture of AES-256 and RSA-2048 ciphers to lock up files by adding the .cnmhr or .jrmcu appendix
Nomikon ransomware is a dangerous virus that locks up files by using the combination of AES-256 and RSA-2048 ciphers
Nomikon ransomware is a dangerous virus that locks up files by using the combination of AES-256 and RSA-2048 ciphers
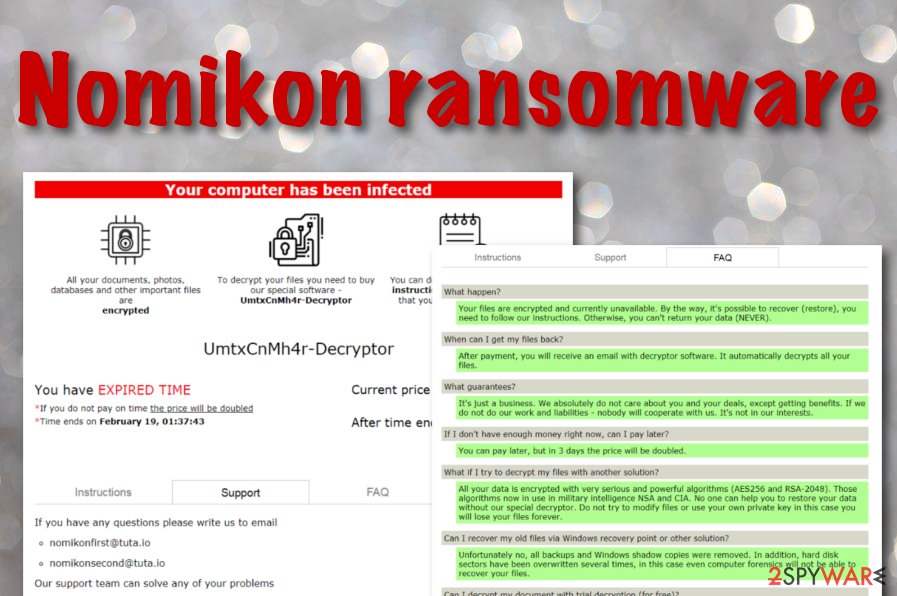
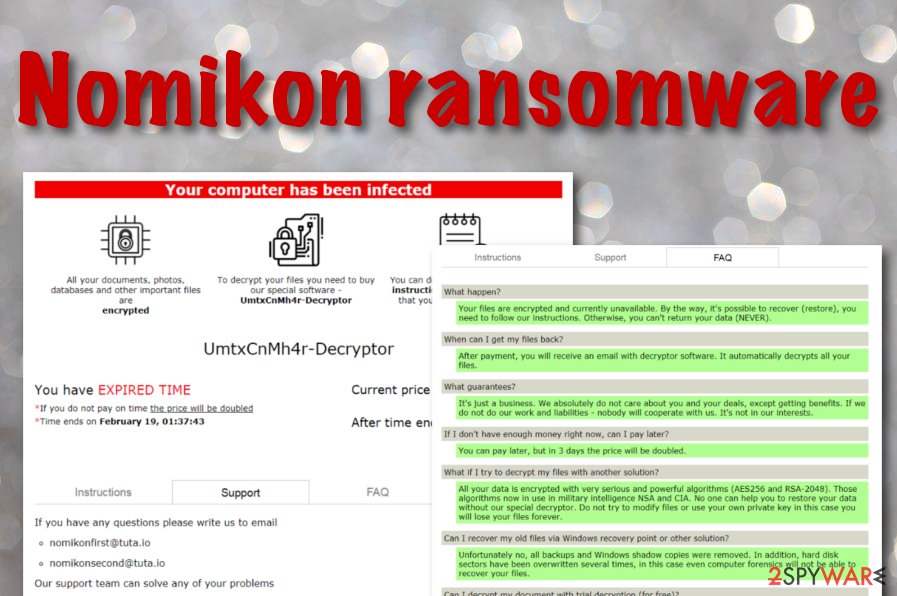
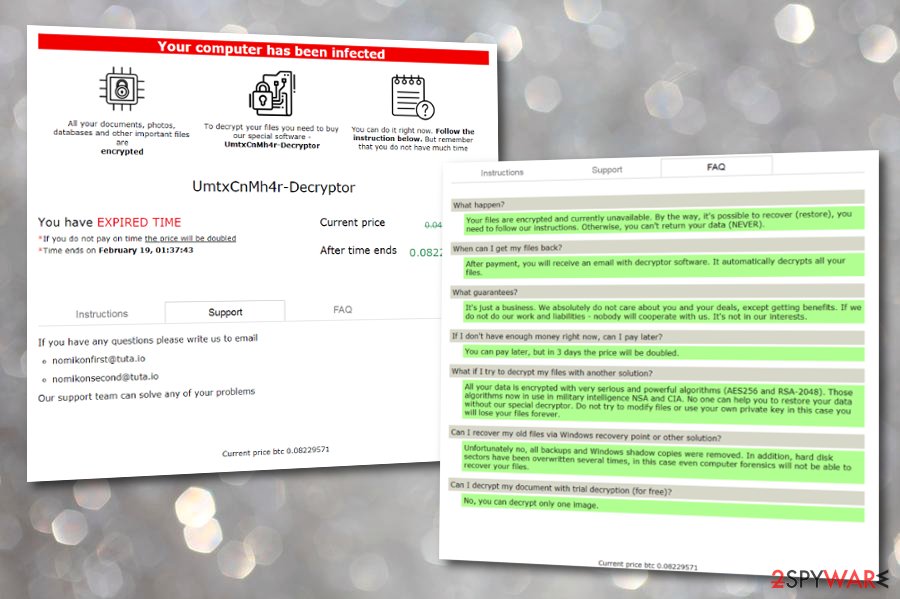
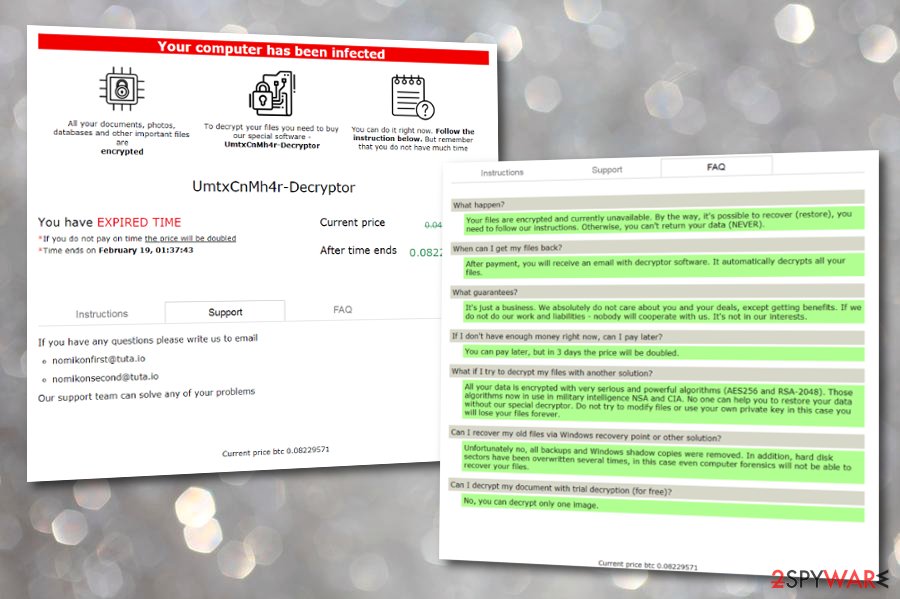
Nomikon ransomware, also recognized as Nomikon 1.0, has been discovered by MalwareHunterTeam to be active since September 2019.[1] Security researchers claim that the malware remained silent since November and has only managed to reach the surface again a few days ago. The main goal of this ransomware infection is to run a combination of AES and RSA ciphers and lock up all the files, documents, and folders that are found lurking on the Windows machine. Right after the encryption, Nomikon ransomware appends the .cnmhr or .jrmcu extension to each filename. Additionally, the cyber threat provides the DECRYPT.html and Your computer has been infected ransom messages where all the payment conditions are revealed.
Nomikon ransomware developers outline that file recovery is only possible by purchasing the decryption tool from them. The virus gives a specific time limit (mostly 3 days) which exceeded doubles the $400 ransom price to $800. The money needs to be transferred in Bitcoin digital currency that starts from 0.04 BTC and can rise up to 0.08 BTC. Also, criminals include the [email protected] and [email protected] emails for contacting them if the victims have any questions. Moreover, these people provide trial decryption that allows recovering one small file for free as evidence that the key is a real one.
| Name | Nomikon ransomware |
|---|---|
| Type | Malware |
| Sub-type | Ransomware virus |
| Extensions | The malware employs AES-256 and RSA-2048 ciphers to lock up all files, folders, and documents that are found on the infected Windows computer system. Afterward, all the components get the .cnmhr or the .jrmcu extension added to their filenames |
| Ransom note(s) | All of the ransom demands, payment conditions and crooks’ contacts are provided in the DECRYPT.html and Your computer has been infected ransom messages. These notes appear after the encryption of files |
| Price demands | Cybercriminals urge a starter price of $400 that is 0.04 in Bitcoin. This type of sum is usually valid for three days and if the victims exceed the time limit, the price doubles to $800 that is 0.08 in Bitcoin cryptocurrency |
| Emails | Hackers provide [email protected] and [email protected] email addresses as a way to make communication between them and the victims |
| Spreading | Most of the time ransomware viruses are distributed through email spam messages and their malicious attachments, vulnerable RDP configuration, software cracks from torrenting websites, and malvertising |
| Elimination | If you are looking forward to getting rid of the ransomware virus, you should complete such a process with a reliable antimalware tool that would be capable of eliminating the dangerous malware |
| Data recovery | If you have not saved any file backups on remote devices, it might be very hard to recover your data. However, paying the demanded price is not a wise option as you can get scammed easily. Diminish the risk of getting tricked and try out some data recovery tools that have been added to the end of this article |
| Fix software | If the ransomware virus has compromised any areas on your Windows computer, you might have a chance of repairing them with the help of software such as Reimage Reimage Cleaner |
Nomikon ransomware is a tricky threat that might not be recognized until files are encrypted and the ransom note is displayed. However, the malware includes malicious processes in the Windows Task Manager where it can pretend to be some type of legitimate software or even a browser application. Furthermore, you might also find new keys included in the Windows Registry[2] that support the ransomware’s functionality.
Nomikon ransomware has the ability to launch its malicious module every time the infected machine is booted. This way the threat ensures its persistence and can repeatedly scan the system for encryptable products. Nevertheless, the malware might include specific tasks or files that block some types of antimalware tools on the attacked device. By employing such technique, Nomikon ransomware can evade antivirus detection.
Nomikon virus – a ransomware infection that has been seen active since September
Nomikon virus – a ransomware infection that has been seen active since September
Afterward, the encryption process begins by using unique codes built by AES-256 and RSA-2048 ciphers. Nomikon ransomware locks up all data such as images, videos, audios, databases, text sheets, word documents, powerpoints, etc. If you recently had a file named myhouse.jpg, its name would be converted to myhouse.jpg.cnhmr or myhouse.jpg.jrmcu. From now on, the data is hardly decryptable, unless you have its backups stored on remote devices.
Nomikon virus developers will try to convince you to make the Bitcoin payment as soon as possible as they are orientated only in receiving money and do not care about your worries. Here comes the risk of getting scammed and being left with no decryption tool. Nevertheless, it seems like the malware aims to harden the recovery process for users by deleting backups that were stored in a place connected to the infected PC, eliminating Shadow Volume Copies,[3] and even overwriting hard disk sectors multiple times:
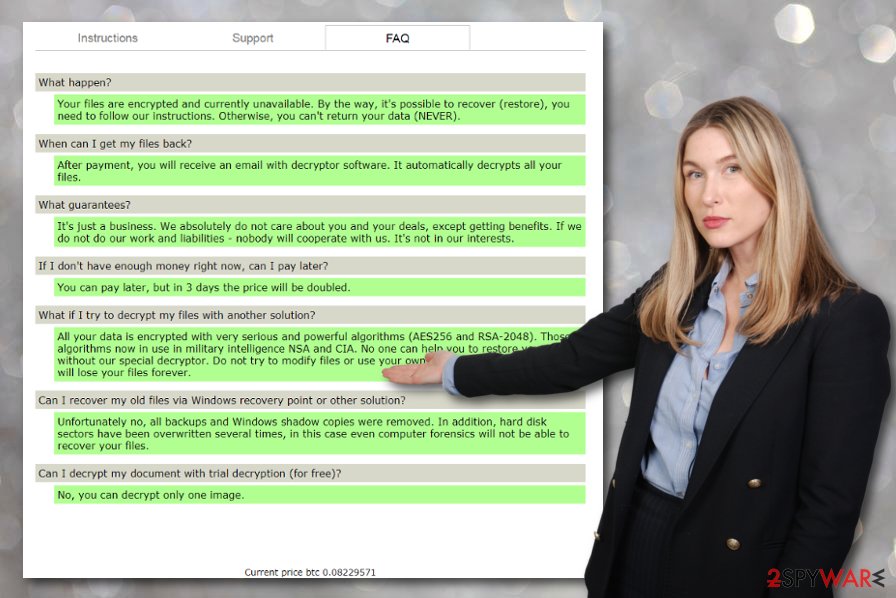
What Happen ?
Your files are encrypted and currently unavailable. By the way, it’s possible to recover (restore), you need to follow our instructions.Otherwise, you can not return your data (NEVER).
When can I get my files back?
After payment, you will receive an email with decryptor software. It automatically decrypts all your files.
What guarantees?
It’s just a business. We absolutely do not care about you and your deals, except getting benefits. If we do not do our work and liabilities – nobody will cooperate with us. It’s not in our interests.
If I do not have enough money right now, can I pay later?
You can pay later, but in three days the price will be doubled.
What if I try to decrypt my files with another solution?
All your data is encrypted with very serious and powerful algorithms (AES256 and RSA- 2048). Those algorithms now in use in military intelligence NSA and CIA. No one can help you to restore your data without our special decryptor. Do not try to modify files or use your own private key in this case you will lose your files forever.
Can I recover my old files via Windows recovery point or other solution?
Unfortunately no, all backups and Windows shadow copies were removed. In addition, hard disk sectors have been overwritten several times, in this case even computer forensics will not be able to recover your files.
Can I decrypt my document with trial decryption (for free)?
No, you can decrypt only one image.Current price btc 0.08229571
Nomikon ransomware stores both encryption and decryption keys on remote servers that can be accessed only by hackers themselves. Even though there are small chances that any other tool would help you to restore at least some of your files, it is better to take that opportunity rather than risking to pay a big amount of money and end up with nothing for it or with fake decryption software in your hands.
Nomikon ransomware might land on your computer system already with additional malware or it can open backdoors for some other cyber threats while lurking on your machine. If this happens, you might end up with a trojan infection or another notorious parasite and get your system damaged, private information stolen, software corrupted, and experience many other malicious and unexpected activities.
Due to all the risks and negative effects that are brought by ransomware viruses, you should remove Nomikon ransomware as soon as you find the encrypted files. Such type of elimination process requires using automatical software that is strong enough to deal with the malware. Also, if your computer has suffered any damage due to the malware infection, you can try recovering the corrupted areas with the help of software such as Reimage Reimage Cleaner .
If you are having some trouble with Nomikon ransomware removal, the malware might be blocking your antivirus tool and in order to diminish such process, you might have to reboot your computer in Safe Mode with Networking and try to eliminate the ransomware again. When the cyber threat is gone, you can try restoring at least some of your files and documents by employing third-party software that is provided at the end of this article.
Most popular delivery techniques of ransomware-related payload
Ransomware infections are spread secretly as if anybody would know that there is malicious payload lurking, they would definitely not opt for its download. In most cases, cybercriminals include malware-laden content into email spam messages in the form of a hyperlink or an attached file. Crooks pretend to come from reputable companies such as DHL or FedEx in order to increase their chances of tricking a big variety of people.
If you ever receive an email message that you were not expecting to get, you should beware that it might be sent by malicious actors. In case of this possibility, you should not press on any hyperlinks that are included in the email and do not open any attached files without scanning them with antimalware software. However, this is not the only way to protect yourself from malware. You should also:
- Avoid using torrenting services for your downloads. A lot of cracked products, especially, key generators, come infected with malware and wait for potential victims to install them.
- Beware not to press on every ad that you see. Malvertising is also a way to deliver malware through tricky advertisements that can be viewed on third-party sources.
- Protect your RDP with proper passwords. Do not keep your RDP configuration vulnerable, always include a password that contains letters, numbers, and even symbols. More complex passwords are harder to breakthrough.
The automatical removal process of Nomikon ransomware
According to technology specialists from Virusai.lt,[4] all ransomware-related components have to be cleaned from the Windows computer system in order to succeed in the elimination properly. Regarding this purpose, you should remove Nomikon ransomware only with the help of reliable antivirus products, otherwise, you might skip some crucial material or make damaging mistakes that can harm your system.
If you are having trouble with Nomikon ransomware removal, this might be because your antivirus software is getting blocked by the malware. To diminish all malicious changes on your Windows PC, you should boot the machine in Safe Mode with Networking. Afterward, return to the elimination process.
When you get rid of Nomikon virus from the machine, you can start thinking about ways to recover your encrypted files. Even though no official decryption key has yet been released for the locked documents, there are other alternative products some of which you can try. To find them, go to the end of this article.
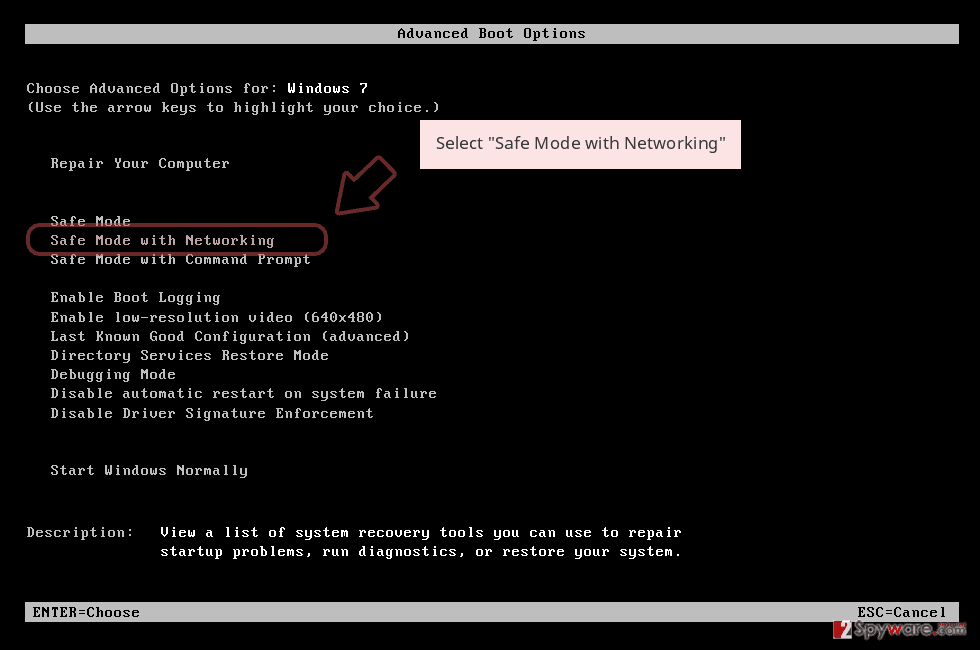
Remove Nomikon using Safe Mode with Networking
To get rid of malicious changes on your Windows computer and disable the parasite, you should try opting for Safe Mode with Networking as described below
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
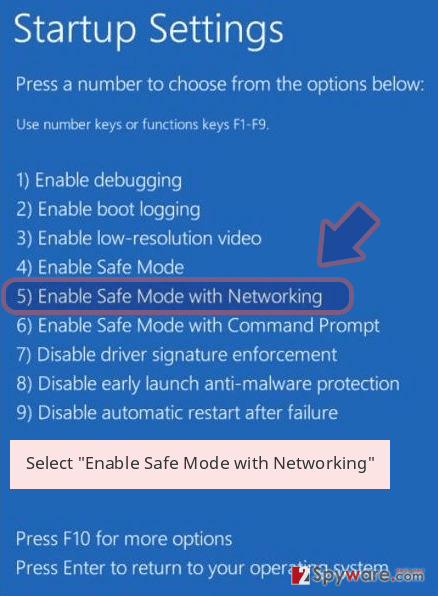
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Nomikon removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Nomikon using System Restore
To deactivate all malware-laden processes on your machine and disable the ransomware virus, you should try launching System Restore on your Windows PC
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Nomikon from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
Files that are encrypted by Nomikon ransomware are very hard to reverse back to their previous states unless you have the official decryption key. However, it is better to try some third-party recovery software rather than risking to get ripped off while paying the demanded ransom price.
If your files are encrypted by Nomikon, you can use several methods to restore them:
Using Data Recovery Pro might help you to save some files
If the ransomware virus has locked, corrupted, or deleted your files and documents, you might have a chance of recovering them with this piece of software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Nomikon ransomware;
- Restore them.
Windows Previous Versions can help to recover some data
If you have been looking for a tool that would help you to recover at least some of the encrypted files, this one might work. However, you need to make sure that you have booted via System Restore before the cyber attack emerged.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Try Shadow Explorer for encrypted documents
If there are some encrypted files on your computer that you want to try to recover, this software might do its job. However, if the ransomware virus has permanently deleted the files’ Shadow Volume Copies, this method will likely not work
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Cybersecurity experts are still working on the official decrypter
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Nomikon and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-02-24 at 06:24 and is filed under Ransomware, Viruses.

